TL;DR:
- Most Queensland SMEs plan to increase cybersecurity investments, emphasizing the importance of regular security reviews. These reviews, including risk assessments, vulnerability scans, and penetration tests, help identify weaknesses, ensure compliance, and improve resilience against cyber threats. Conducting consistent, scoped assessments and acting on findings develops a security culture, reducing risk and protecting business continuity.
Ninety-four percent of SMEs are planning to increase their cybersecurity investment, which signals something important: cyber threats are no longer a big-business problem. Queensland small and medium enterprises are firmly in the crosshairs of cybercriminals, and the businesses that survive attacks are typically those that have already identified their weaknesses before a threat actor does. Regular security reviews are the most practical tool you have to stay ahead of that curve, protect your customers’ trust, and keep your operations running without interruption.
Table of Contents
- What does a regular security review involve?
- Why regular reviews matter: Key business benefits
- How often should you review your security?
- Making security reviews practical: Steps for Queensland SMEs
- What most advice misses about security reviews
- Take the next step with expert security support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Regular reviews prevent threats | Frequent security reviews help SMEs spot vulnerabilities before attackers do. |
| Tailor reviews to your goals | Choose the type of assessment based on your business needs, not just compliance checkboxes. |
| Combine reviews with staff training | Linking your technical defences with regular team education offers the strongest protection. |
| Use local tools and support | Queensland-specific resources simplify the review process and boost your cyber readiness. |
What does a regular security review involve?
Regular security reviews are not a single event. They are a collection of structured activities designed to give your business an accurate picture of where your risks sit, what your defences can handle, and where your gaps need urgent attention.
There are four main types of review that Queensland SMEs should understand:
| Review type | Purpose | Recommended frequency | Who conducts it |
|---|---|---|---|
| Risk assessment | Identifies and prioritises business risks | Annually or after major changes | Internal team or IT partner |
| Vulnerability scan | Detects known weaknesses in systems and software | Quarterly or monthly | IT provider or automated tool |
| Penetration test | Simulates a real attack to find exploitable gaps | Annually or biannually | Specialist security firm |
| Governance, risk and compliance (GRC) review | Checks alignment with regulations and frameworks | Annually, or as regulations change | Compliance specialist or IT partner |
Each review type serves a different purpose, and the smartest Queensland SMEs use a combination rather than relying on just one.
A standard security review typically covers several core tasks:
- Mapping all devices, software, and data assets connected to your network
- Checking for unpatched software, outdated firmware, and misconfigured systems
- Reviewing user access permissions to ensure staff only see what they need
- Testing your cyber incident response plans to confirm they actually work under pressure
- Evaluating physical security controls like building access and device storage
- Reviewing staff security training records to ensure your people know what to watch for
- Generating a written findings report with prioritised recommendations
Business Queensland recommends ongoing cyber security measures including staff training, incident response planning, and using security assessment tools like the Cyber Health Check to improve overall readiness. This free tool is a sensible starting point for any Queensland SME that has not yet formalised its security review process.
Pro Tip: Choose your review type based on your immediate goal. If you need to satisfy a compliance requirement, a GRC review is your priority. If you want to understand how your defences hold up against real attacks, invest in a penetration test. If you simply want a clear risk picture, a risk assessment is the right place to start.
Why regular reviews matter: Key business benefits
Understanding what a review involves sets the foundation. Now let’s connect that directly to your business outcomes, because the case for regular security reviews goes well beyond avoiding fines.
The Hiscox Cyber Readiness Report confirms that the vast majority of SMEs plan to increase security investment, with frequent risk assessments and vulnerability checks forming a core part of that proactive posture. That shift in attitude is not accidental. It reflects what business owners across industries are learning the hard way: a single incident can cost more than years of preventive investment.
Here is why regular reviews pay off in concrete terms:
- Prevent incidents before they happen. Reviews surface vulnerabilities while they are still manageable. A misconfigured firewall or an outdated server discovered during a review costs a fraction of what a breach costs after the fact.
- Maintain regulatory compliance. Industries like financial services, healthcare, and legal services face strict data handling obligations in Queensland. Reviews verify you are meeting those requirements before an auditor or a regulator does it for you.
- Reduce costly downtime. Ransomware attacks can lock your business out of critical systems for days or weeks. Reviews that identify backup failures and weak endpoints dramatically reduce that exposure.
- Protect your reputation. Customers and partners in Queensland increasingly ask about security practices before signing contracts. A documented review history signals that your business takes data protection seriously.
- Support cyber insurance eligibility. Insurers are tightening their requirements. Many now ask for evidence of recent security assessments before issuing or renewing policies. Regular reviews keep you eligible and can reduce your premiums.
- Detect insider threats early. Access control reviews and activity monitoring, components of a proper security assessment, catch unusual behaviour patterns that might indicate a disgruntled employee or a compromised account.
If you are unsure whether your current situation warrants immediate attention, reviewing the signs you need cyber security intervention is a worthwhile first step.
“The cost of inaction is not just financial. A business that suffers a preventable data breach faces regulatory scrutiny, customer churn, and reputational damage that can take years to recover from. For SMEs without the capital reserves of large enterprises, that recovery window may not exist.”
Regular reviews build resilience step by step. They create a feedback loop where each assessment informs the next, your defences improve incrementally, your team grows more security-conscious, and your business becomes a harder target over time.
How often should you review your security?

Once you see the value in regular reviews, the next question is how often your business should schedule them. The honest answer is that it depends on your risk profile, your regulatory obligations, and how heavily your operations rely on digital systems.
Here is a practical comparison framework:
| Business profile | Vulnerability scan | Risk assessment | Penetration test | GRC review |
|---|---|---|---|---|
| Basic (low digital dependency) | Twice yearly | Annually | Every 2 years | When regulations change |
| Mature (moderate digital reliance) | Quarterly | Annually | Annually | Annually |
| Regulated (finance, health, legal) | Monthly | Biannually | Annually | Biannually |
Beyond scheduled reviews, certain trigger events should prompt an immediate ad hoc assessment:
- A major technology upgrade. Moving to a new cloud platform, deploying new software, or migrating data all introduce new risks that your existing controls may not cover.
- A regulatory or compliance change. New legislation affecting your industry can create overnight compliance gaps. A targeted GRC review confirms you are meeting the updated requirements.
- A near-miss or actual security incident. Even a minor phishing attempt that was caught should prompt a review to understand whether your defences held for the right reasons.
- Significant staff changes. Onboarding or offboarding key people with system access, especially in senior or technical roles, warrants an access control review.
- Expansion into new markets or services. Growth often introduces new data handling requirements and technology integrations that need security scrutiny.
The recommended assessment frequency for most Queensland SMEs is at least annual, with vulnerability scans running more frequently depending on your digital footprint. For businesses in regulated industries or those with significant continuity planning needs, a biannual risk assessment cycle is strongly advisable.
The Hiscox report reinforces that businesses with a proactive review posture consistently outperform their peers in incident prevention rates and recovery speed, which makes the frequency question less of a cost calculation and more of a business survival decision.
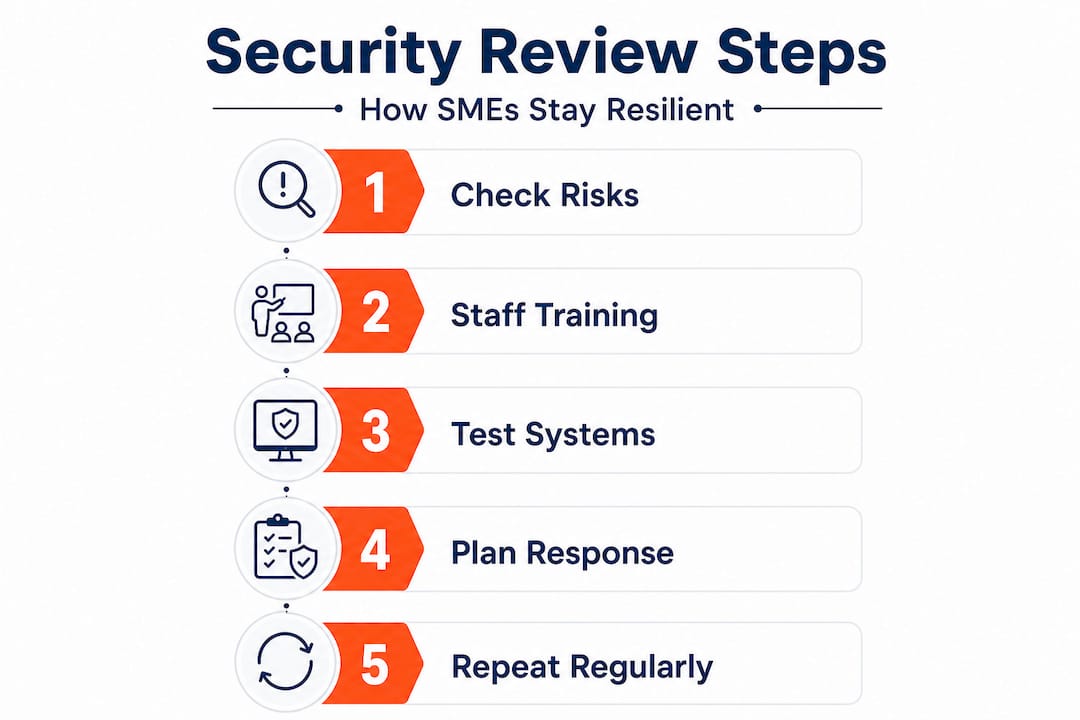
Making security reviews practical: Steps for Queensland SMEs
With timing and frequency clear, adopting security reviews becomes all about practical steps. The most common reason Queensland SMEs skip reviews is not cost or complexity. It is the absence of a clear, repeatable process that fits into a busy business routine.
Here is how to make security reviews a consistent practice rather than a once-in-a-blue-moon event:
- Assign clear accountability. Designate one person, whether internal or an external IT partner, as responsible for scheduling, tracking, and reporting on security reviews. Without a named owner, reviews get postponed indefinitely.
- Use simple tools to get started. Business Queensland’s Cyber Health Check is a no-cost, structured way to benchmark your current security posture and identify the highest-priority gaps without needing technical expertise.
- Combine reviews with training. Running staff education sessions alongside or immediately after a security review reinforces findings with real context. People are far more receptive to training when they can see why it matters to their specific role and environment.
- Document everything. Keep a written record of findings, recommendations, and actions taken. This documentation is invaluable for insurance claims, regulatory audits, and demonstrating due diligence to clients.
- Act on findings within a defined timeframe. A review that generates a report and no action is worse than no review at all. It creates a paper trail showing you knew about a weakness and chose not to address it. Set a 30, 60, or 90-day remediation window for each finding based on severity.
- Schedule the next review before you close the current one. Book the follow-up assessment date before you file the current report. This simple habit eliminates the gap that allows risks to accumulate unnoticed.
Business Queensland specifically recommends that SMEs use the Cyber Health Check tool and pair it with staff training and incident response preparation for a well-rounded, ongoing security posture. The practical cyber security guide for Brisbane SMEs gives further detail on how to turn these steps into an embedded routine.
Pro Tip: The Queensland Government’s Cyber Health Check is free and takes under an hour to complete. Use it as your baseline before investing in paid assessments. It will help you prioritise where professional support will add the most value and make any conversation with a security partner far more productive. You can also review staff cyber training tips to build your team’s awareness alongside the technical controls.
What most advice misses about security reviews
Pulling together everything we have covered, it is important to separate genuine best practice from common misconceptions that quietly undermine Queensland SMEs’ security efforts.
The most persistent myth is that all security reviews are interchangeable, that running any kind of assessment once a year is enough to satisfy both compliance and operational resilience needs. That logic leads businesses to run vulnerability scans when they actually need a penetration test, or to conduct risk assessments when a GRC review is what their regulator actually requires.
Penetration tests, vulnerability scans, and governance risk reviews are complementary rather than interchangeable. The right choice depends entirely on whether you need compliance evidence, maturity and effectiveness insight, or adversarial vulnerability discovery. Treating them as equivalent produces a false sense of security that can be more dangerous than no review at all.
The second major oversight in most advice is the assumption that a security review is a standalone event rather than part of a continuous improvement cycle. The businesses we see genuinely improve their resilience over time are the ones that treat each review as input into the next one. They track trends, monitor whether previously identified issues have actually been resolved, and adjust their review frequency based on what the data is telling them.
There is also the human element, which almost every checklist-style guide underplays. Technical controls are only as effective as the people operating them. A firewall misconfigured by an untrained staff member is a liability, not an asset. Integrating security reviews with staff education and engagement transforms what could be a dry compliance exercise into a genuine culture shift.
The smartest move for a Queensland SME is not to schedule the most exhaustive review possible once every few years. It is to schedule focused, appropriately scoped reviews on a recurring basis, act on findings immediately, and build that discipline into your real-world security planning from the ground up.
Regular and purposeful always beats sporadic and exhaustive.
Take the next step with expert security support
If this article has reinforced that your business needs a more structured approach to security reviews, IT Start can help you get there without the overwhelm. We work with Queensland SMEs across Brisbane and beyond to design and deliver recurring security assessments that match your risk profile, your industry requirements, and your budget. Our approach combines expert cyber security services with practical staff training and, where needed, cloud security support to address vulnerabilities across your entire environment. Whether you are starting from scratch or looking to mature an existing programme, we tailor our support to where your business actually is. Reach out today for a no-obligation conversation about your security review schedule.
Frequently asked questions
What is the first step in a security review for Queensland SMEs?
Start by assessing your current risks using the free Cyber Health Check provided by Business Queensland, then use the results to prioritise your highest-priority gaps before investing in more advanced assessments.
How often should an SME update its security review?
Most SMEs should conduct a formal review at least annually, but SME benchmark data shows that businesses with a proactive posture run vulnerability checks quarterly and trigger additional reviews after any significant change to their IT environment.
What types of security assessments should SMEs consider?
You should consider risk assessments, vulnerability scans, penetration tests, and compliance reviews, selecting the right type based on your goals. As security experts note, these assessment types are complementary rather than interchangeable, so matching the tool to the objective is essential.
Does regular staff training lower cyber risk?
Yes, significantly. Business Queensland recommends staff training as an ongoing defence measure because human error remains one of the leading causes of successful cyber incidents for SMEs.



