TL;DR:
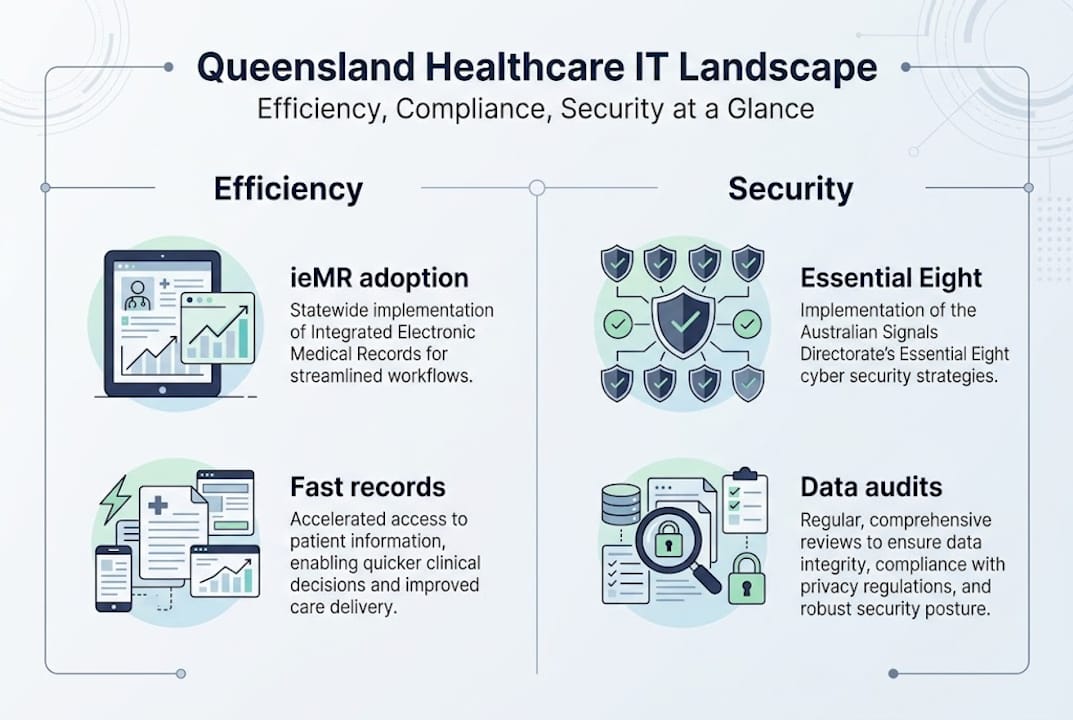
- Most Queensland health facilities have upgraded IT systems but still face operational, compliance, and cybersecurity challenges.
- Digital tools like ieMR improve patient flow, reduce inpatient stays, and enhance operational visibility.
- Effective IT governance, phased adoption, and cybersecurity measures are essential for sustainable, secure healthcare IT.
Most Queensland health facilities have recently upgraded their IT systems, yet operational bottlenecks, compliance gaps, and cybersecurity vulnerabilities continue to cost money and put patients at risk. 78% of Queensland health facilities upgraded IT systems in the past 18 months, yet the hard work of translating that investment into reliable, secure, and compliant operations is still unfinished. For healthcare administrators and practice managers across Queensland, the challenge is not simply buying new technology. It is making that technology work safely, consistently, and in line with both state and national requirements. This guide cuts through the noise and gives you a clear, practical roadmap.
Table of Contents
- How IT transforms operational efficiency in Queensland healthcare
- Meeting compliance and data governance standards
- Cybersecurity risk: The Essential Eight and beyond
- Overcoming practical challenges: Legacy systems, remote areas, and audits
- The real-world path to sustainable, secure IT in Queensland healthcare
- How we help Queensland healthcare facilities thrive
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| IT delivers efficiency | Digital solutions like ieMR drive faster, safer patient care and reduce hospital stays. |
| Compliance must be local | Administrators should align ICT policy with both Queensland and national health standards for legal safety. |
| Cybersecurity is essential | Implement the ACSC Essential Eight to shield against costly breaches and regulatory penalties. |
| Legacy challenges persist | Ongoing upgrades and staff engagement are crucial for remote, rural, and legacy system environments. |
| Expert help accelerates success | Specialist IT support helps Queensland healthcare facilities navigate technology, compliance, and security confidently. |
How IT transforms operational efficiency in Queensland healthcare
With investment levels high, let us explore how IT is driving real operational improvements across Queensland facilities.
Digital platforms like the integrated electronic Medical Record (ieMR) and broader electronic health record (EHR) integration have fundamentally changed how patient information moves through a facility. Rather than paper-based handovers and siloed departmental records, clinicians now access unified patient histories in real time. Digitising Patient Flow directly targets reductions in inpatient length of stays, which is one of the most expensive inefficiencies in any hospital system. Fewer days in a bed means more capacity for incoming patients and lower cost per episode of care.
The numbers behind Queensland’s health system make this scale clear:
| Metric | Figure |
|---|---|
| Annual inpatient admissions | 1.6 million+ |
| Facilities with recent IT upgrades | 78% |
| Primary driver of IT investment | Operational efficiency and patient safety |
| Key platform in rollout | ieMR (integrated electronic Medical Record) |
Beyond admissions, IT improvements are creating better visibility across emergency department throughput and surgical scheduling. Administrators can now monitor bottlenecks in near real time using performance benchmarks published by Queensland Health, which allows faster reallocation of staff and resources before a backlog becomes a crisis.
However, the gains are uneven. Metro facilities with dedicated IT teams tend to adopt new systems faster and more thoroughly than rural or remote sites. Legacy infrastructure, including outdated servers, unsupported operating systems, and poorly integrated third-party software, slows rollouts and creates parallel workflows that frustrate staff. When a nurse has to use two separate systems to complete one patient record, efficiency gains evaporate quickly.
Key areas where IT delivers measurable operational improvement include:
- Automated patient flow tracking reducing manual handover delays
- Centralised scheduling tools cutting double-bookings and gaps in theatre use
- Digital discharge summaries speeding up bed turnover
- Real-time reporting dashboards giving administrators instant visibility
Pro Tip: When prioritising IT projects, focus first on changes that produce quick, visible wins for frontline staff. Optimising IT workflows at the process level, before adding more technology, often delivers faster results than a full system replacement.
Meeting compliance and data governance standards
Efficient operations depend on compliance, and here is what Queensland facilities need to know.
Queensland Health operates within a layered compliance environment. At the national level, the Privacy Act 1988 and the My Health Records Act 2012 set the baseline for how patient data must be collected, stored, accessed, and disclosed. Queensland then adds its own layer through the Queensland Health ICT Policy Framework, which translates national obligations into state-specific directives, standards, and procedures.
Mandatory digital policies are reviewed on a three-year cycle, but additional directives can be introduced at any time in response to emerging risks or legislative changes. This means your compliance calendar cannot be set-and-forget. Practice managers need a live register of applicable policies and a nominated person responsible for monitoring updates.
A key feature of Queensland’s approach is co-design. New ICT policies are developed in collaboration with Hospital and Health Services (HHSs) across the state, which means local operational realities are factored into the standards. That is good news for administrators, but it also means you are expected to actively participate in consultation processes rather than simply receiving instructions from above.
| Requirement | Queensland-specific | National baseline |
|---|---|---|
| Policy framework | Queensland Health ICT Policy Framework | Privacy Act 1988 |
| Health records | Queensland Health directives | My Health Records Act 2012 |
| Review cycle | Every 3 years (mandatory) | As legislated |
| Governance body | HHSs via co-design | OAIC, ADHA |
| Audit readiness | Facility-level documentation required | Notifiable Data Breaches scheme |
For practice managers, the practical obligations come down to four areas:
- Access control: Who can view, edit, or export patient records, and is that list current?
- Documentation: Are your data handling procedures written, version-controlled, and accessible to staff?
- Audit readiness: Can you produce evidence of compliance at short notice?
- Incident response: Do you have a documented process for protecting patient data in the event of a breach?
The cost of non-compliance is not just financial. A breach that exposes patient records can damage community trust in ways that take years to rebuild.
Cybersecurity risk: The Essential Eight and beyond
Compliance dovetails closely with cybersecurity, where Queensland’s risk profile is unique.
Healthcare is one of the most targeted sectors for cyberattack globally, and Australian facilities are no exception. Patient records contain a dense combination of personal, financial, and medical information, making them extremely valuable on criminal markets. A single compromised record can sell for many times the value of a stolen credit card.
The Australian Cyber Security Centre (ACSC) developed the ACSC Essential Eight as a practical, government-backed baseline to protect organisations from the most common attack vectors. For Queensland healthcare facilities, this framework is not optional guidance. It is the recommended minimum standard.
The Essential Eight framework covers eight mitigation strategies:
- Application control: Only approved software runs on your systems
- Patch applications: Known vulnerabilities in software are fixed promptly
- Configure Microsoft Office macro settings: Malicious macros cannot execute automatically
- User application hardening: Browsers and email clients are locked down
- Restrict administrative privileges: Admin access is limited to those who genuinely need it
- Patch operating systems: OS vulnerabilities are addressed within defined timeframes
- Multi-factor authentication (MFA): Login requires more than just a password
- Regular backups: Data can be restored after an incident
Each strategy has four maturity levels (zero through three). Most healthcare facilities should target at least Maturity Level Two across all eight strategies.
The three highest-impact starting points for most Queensland clinics are MFA, regular patching, and tested backups. These three controls alone block the majority of ransomware attacks.
Common pitfalls include legacy systems that cannot support modern patching schedules, and overly broad user access permissions that were set up years ago and never reviewed. Understanding cybersecurity essentials for healthcare and applying practical security tips tailored to your environment will help you prioritise where to spend limited IT budgets.
Pro Tip: Request a copy of your most recent internal or external IT audit findings. The specific deficiencies listed there are your highest-priority cybersecurity investments, not a generic checklist.
Overcoming practical challenges: Legacy systems, remote areas, and audits
Practical implementation exposes gaps even the best policies cannot prevent. How do facilities get around them?
Legacy IT is the single biggest barrier to progress in Queensland healthcare. Older systems were not designed to integrate with modern platforms, and replacing them is expensive, disruptive, and risky. The RIVeR system rollout in Far North Queensland drew direct criticism from clinicians and health unions due to safety concerns, illustrating that poorly managed transitions can create new risks rather than solving old ones. Earlier, Queensland’s payroll system failure cost an estimated $1.2 billion, a stark reminder that IT governance failures carry real financial consequences.
Remote and Indigenous communities face compounding challenges. Workforce gaps mean fewer trained IT staff on site. Network infrastructure is often limited, making cloud-based solutions unreliable without significant investment in connectivity. Cultural and language considerations also affect how digital tools are adopted and used by both staff and patients.
Audit findings from Queensland Health consistently identify IT access control deficiencies and delayed remediation as recurring issues, meaning the same problems appear year after year without resolution.
The Queensland Health audit report confirms that IT and security control improvements remain an ongoing priority, with access management and timely patching flagged as areas needing attention. Administrators who treat audit recommendations as a compliance formality rather than an action list are leaving their facilities exposed.
A practical approach to managing these challenges:
- Map your legacy systems and document which are end-of-life or unsupported
- Prioritise internet risk management by reviewing internet risk management strategies suited to healthcare environments
- Stage your migrations rather than attempting full replacement in one go
- Invest in staff training before and during any system transition, not just after
- Create exception registers for systems that cannot be immediately upgraded, with documented compensating controls
- Review access permissions quarterly, not annually
The facilities that navigate legacy challenges most successfully are those that treat IT governance as an ongoing operational discipline rather than a project with a finish line.
The real-world path to sustainable, secure IT in Queensland healthcare
Here is what often gets missed in boardroom and government strategies.
After years of working with healthcare organisations across Queensland, one pattern stands out clearly: the facilities that achieve lasting IT improvements are not the ones with the biggest budgets. They are the ones that connect technology decisions to frontline staff experience from the very beginning.
Government strategies and vendor pitches tend to focus on capability and compliance. What they undervalue is adoption. A system that clinicians work around is worse than no system at all, because it creates parallel processes, data gaps, and hidden risks. Co-design is not just a policy requirement. It is the difference between a tool people use and one they resent.
The counterintuitive reality is that staged adoption often outperforms expensive full transformation. A phased rollout allows staff to build confidence, IT teams to identify integration problems early, and administrators to demonstrate value before committing further resources. Chasing the cybersecurity reality for Queensland clinics means accepting that perfect security is never achieved in one step. Consistent, incremental progress beats ambitious plans that stall under their own weight.
How we help Queensland healthcare facilities thrive
Having explored practical ways to optimise IT, here is how expert help can support your next move.
At IT Start, we work with Queensland healthcare practices to align IT infrastructure with operational goals, compliance obligations, and cybersecurity requirements. Whether you are managing a busy Brisbane clinic or a multi-site regional practice, our team brings local knowledge and certified expertise to every engagement. Our cloud services for healthcare support secure, scalable data access across locations. Our healthcare cyber security services are built around the Essential Eight framework, giving you a structured path to stronger defences. If you are ready to take the next step, speak with our consultants for a no-obligation assessment of your current IT environment.
Frequently asked questions
What is ieMR and how does it benefit Queensland healthcare?
ieMR (integrated electronic Medical Record) streamlines patient management by digitising patient flows, reducing duplication, and improving clinical outcomes across Queensland facilities.
How often do Queensland Health IT policies and compliance standards change?
Mandatory digital policies are reviewed every three years, but additional directives can be introduced at any time in response to new risks or legislative changes.
What is the Essential Eight and why is it vital for clinics?
The ACSC Essential Eight is a government-backed cybersecurity framework that provides healthcare facilities with a practical baseline to defend against ransomware, data breaches, and unauthorised access.
How can IT improve performance in remote or rural Queensland clinics?
New systems can improve real-time data access and reduce clinical errors, but legacy platforms and network limitations in remote areas require tailored, staged solutions rather than a one-size-fits-all approach.



