Queensland’s small and medium businesses face mounting pressure from escalating data breaches and evolving compliance obligations. Many SMB owners mistakenly view IT as merely a technical function, overlooking its strategic role in meeting legal duties and protecting customer trust. This guide clarifies how IT drives compliance across organisational levels, explains Queensland’s IS18 policy influence, and provides practical steps to strengthen your business’s compliance posture. You’ll discover actionable frameworks, real-world examples, and expert insights tailored for Brisbane businesses navigating 2026’s complex regulatory landscape.
Table of Contents
- How IT Supports Compliance Across Multiple Organisational Levels
- Queensland Government’s IS18 Policy And Its Influence On SMB IT Compliance
- The ADITS And Pax8 Partnership: A Case Study In IT-Driven Compliance Solutions For SMBs
- Practical IT Strategies For Queensland SMBs To Achieve Compliance And Reduce Risk
- How IT Start Can Support Your SMB’s Compliance Journey
Key takeaways
| Point | Details |
|---|---|
| Multi-layered compliance | IT security requirements operate across executive, operational, and technical levels within your organisation. |
| Queensland IS18 influence | The IS18 policy sets government standards that shape SMB cybersecurity practices and resilience expectations. |
| MSP partnership value | Managed service providers deliver compliance tools, training, and ongoing monitoring to reduce risk. |
| Rising breach urgency | Data breaches increased 25%, making proactive IT compliance essential for SMB survival. |
| Practical implementation | Assessment tools, staff training, and expert guidance enable SMBs to meet compliance obligations efficiently. |
How IT supports compliance across multiple organisational levels
IT compliance involves operationalising security requirements across multiple organisational levels, not just installing software or updating systems. Your executive team sets strategic direction and risk appetite. Your IT department translates those decisions into technical controls and monitoring systems. Your operational staff execute daily processes that either strengthen or undermine compliance efforts.
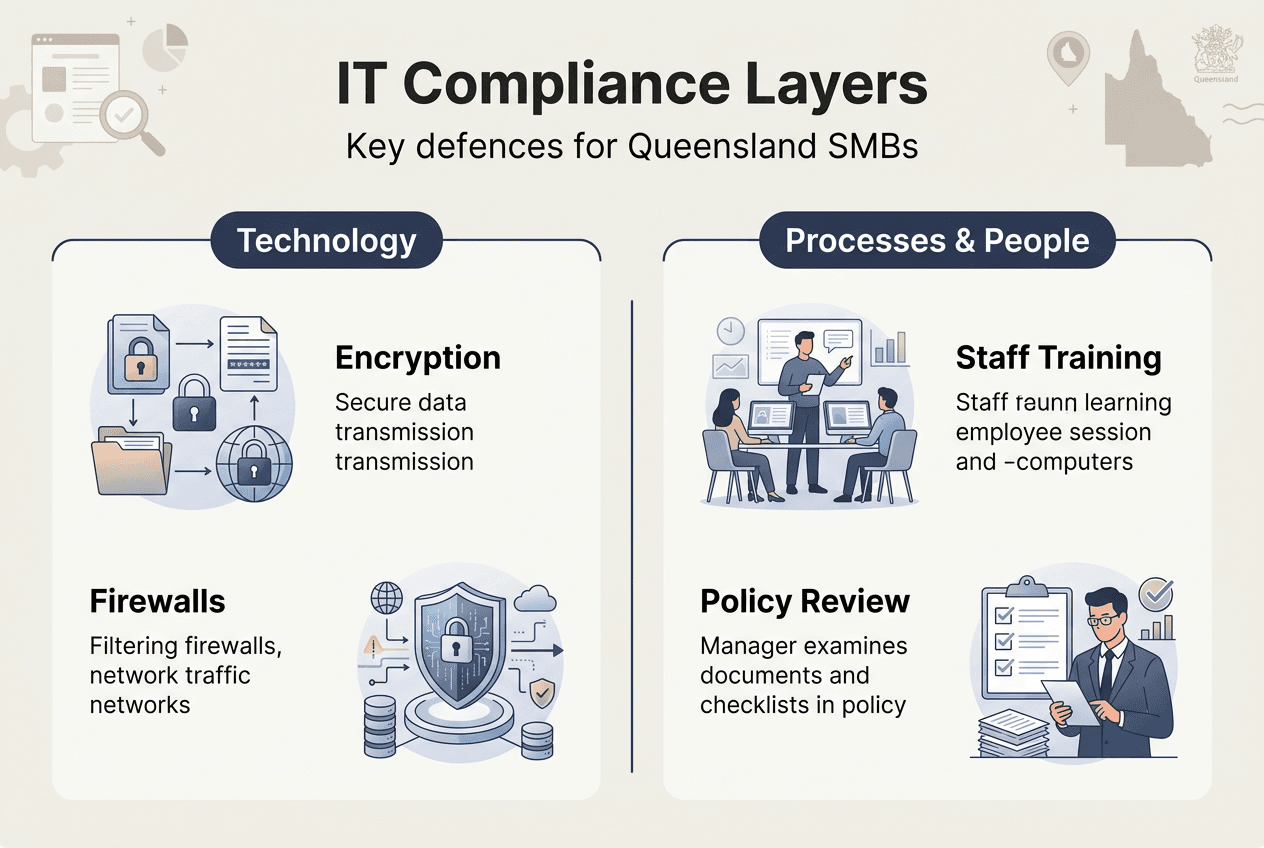
Each level requires distinct yet interconnected compliance activities. Executives approve policies and allocate budgets for security investments. IT teams implement firewalls, encryption, access controls, and vulnerability management. Operations personnel follow data handling procedures, report incidents, and maintain awareness of threats. When these layers work in harmony, your business creates a robust compliance framework that withstands regulatory scrutiny and cyber threats.
Policies, processes, and technology must intersect seamlessly. A data protection policy means nothing without encrypted databases and staff trained to recognise phishing attempts. Similarly, advanced security technology fails when employees bypass controls or executives ignore IT recommendations. IT compliance best practices emphasise this integration, ensuring every organisational layer contributes to your compliance posture.
This multi-layered approach directly impacts daily operations and risk mitigation. When IT compliance functions properly, you reduce breach likelihood, maintain customer trust, and avoid costly regulatory penalties. Your teams work more efficiently because security processes become embedded workflows rather than burdensome add-ons. Data flows securely between departments, audits proceed smoothly, and your business demonstrates due diligence to clients and regulators.
Pro Tip: Map your compliance responsibilities across organisational levels quarterly. Identify gaps where policies lack technical implementation or where operational staff need additional training. This exercise reveals weak points before auditors or attackers discover them.
Common compliance failures occur when businesses treat IT as purely technical. You might invest in expensive security software but neglect staff training. Or your executives might approve policies without understanding implementation costs. Recognising IT’s role across all levels prevents these disconnects and builds genuine compliance capability.
Queensland government’s IS18 policy and its influence on SMB IT compliance
Queensland’s IS18 policy aims to improve protection of services and enhance organisational resilience across government entities. While directly applicable to public sector organisations, IS18 establishes security standards that influence private sector expectations and client requirements. Brisbane SMBs working with government clients or handling sensitive data face increasing pressure to demonstrate comparable security maturity.
The policy emphasises several core objectives relevant to SMBs. Protection of government information extends to contractors and service providers, meaning your business must implement controls matching government standards. Trust enhancement requires transparent security practices and incident response capabilities. Resilience building demands backup systems, disaster recovery plans, and continuous monitoring. These aren’t just government concerns but fundamental business imperatives in 2026’s threat environment.

For SMBs, IS18 creates both challenges and opportunities. You might struggle with resource constraints when implementing government-grade security controls. However, aligning with IS18 principles differentiates your business from competitors and opens doors to government contracts. Many private sector clients now expect similar standards, making IS18 alignment a competitive advantage rather than just a compliance burden.
Key areas deserve your focus when aligning practices with IS18 principles:
- Access control and identity management to ensure only authorised personnel access sensitive systems
- Incident detection and response capabilities to identify and contain breaches quickly
- Regular security assessments and vulnerability testing to maintain defensive posture
- Staff awareness training to build human firewalls against social engineering
- Data classification and handling procedures to protect information appropriately
Cybersecurity policies tailored for Brisbane businesses incorporate IS18 principles while remaining practical for SMB implementation. You don’t need enterprise budgets to achieve meaningful alignment. Focus on foundational controls like multi-factor authentication, encrypted communications, and documented procedures. These basics satisfy most IS18 requirements and protect against common threats.
“The Queensland Government’s IS18 policy establishes a baseline for information security that increasingly influences private sector expectations. SMBs demonstrating comparable security maturity gain competitive advantage and client trust.”
Implementing IS18-aligned practices requires phased execution. Start with risk assessment to identify your most critical assets and vulnerabilities. Prioritise quick wins like password policies and backup verification. Gradually build toward comprehensive controls as resources permit. This pragmatic approach delivers measurable security improvements without overwhelming your team or budget.
The ADITS and Pax8 partnership: a case study in IT-driven compliance solutions for SMBs
ADITS partnered with Pax8 to develop CyberShield, a Privacy Act assessment and cybersecurity tool specifically designed for Queensland SMBs. This partnership demonstrates how managed service providers leverage technology platforms and training to deliver practical compliance solutions. ADITS recognised that many Brisbane businesses struggled with Privacy Act obligations, lacking both expertise and tools to conduct proper assessments.
CyberShield addresses this gap by automating privacy compliance assessments and generating actionable recommendations. The tool evaluates your data handling practices against Privacy Act requirements, identifies vulnerabilities, and prioritises remediation steps. Rather than hiring expensive consultants or attempting DIY compliance, SMBs access professional-grade assessment capabilities at affordable price points. This democratisation of compliance tools levels the playing field for smaller organisations.
Pax8 Academy training played a crucial role in ADITS’s capability development. The platform provided structured learning paths covering cybersecurity fundamentals, compliance frameworks, and solution deployment. ADITS technicians gained expertise in privacy regulations, threat assessment, and client communication. This knowledge transfer enabled them to deliver consultative services beyond basic technical support, positioning ADITS as a strategic compliance partner rather than just an IT vendor.
| Partnership Element | SMB Benefit | Implementation Approach |
|---|---|---|
| CyberShield tool | Automated Privacy Act assessments | Cloud-based platform with guided workflows |
| Pax8 Academy training | Expert guidance from skilled technicians | Structured learning paths and certifications |
| Ongoing support | Continuous monitoring and updates | Managed service agreements with regular reviews |
| Scalable solutions | Cost-effective compliance for growing businesses | Tiered service levels matching business needs |
The benefits of MSP partnerships for compliance readiness extend beyond tools and training. You gain access to collective intelligence about emerging threats and regulatory changes. Your MSP monitors multiple clients, spotting patterns and sharing insights across their customer base. When new vulnerabilities emerge or regulations change, your MSP updates protections proactively rather than waiting for you to request changes.
Pro Tip: When evaluating MSPs for compliance support, ask about their training investments and tool partnerships. Providers investing in platforms like Pax8 Academy demonstrate commitment to expertise development. Request case studies showing how they’ve helped similar Brisbane businesses achieve specific compliance outcomes.
Managed services providers deliver value through specialisation and scale. You avoid hiring full-time security experts or purchasing expensive compliance software. Instead, you share these resources across the MSP’s client base, accessing enterprise-grade capabilities at SMB prices. This model particularly suits Brisbane businesses where talent scarcity makes hiring security specialists challenging and costly.
The ADITS example illustrates how local Queensland providers understand regional compliance nuances. They navigate state-specific regulations, industry requirements, and client expectations shaped by Brisbane’s business environment. This local expertise combined with global best practices creates compliance solutions matching your operational reality. IT compliance guides tailored for Brisbane businesses reflect this localised approach while maintaining rigorous standards.
Practical IT strategies for Queensland SMBs to achieve compliance and reduce risk
Effective compliance and risk management is a strategic framework for spotting threats, meeting legal duties, and building client trust. Queensland SMBs need practical, resource-appropriate strategies that deliver genuine security improvements without requiring enterprise budgets or dedicated compliance teams. The following stepwise approach enables systematic compliance implementation.
- Conduct a comprehensive risk assessment identifying your most valuable data assets and likely threat scenarios
- Document existing security controls and data handling procedures to establish your current baseline
- Compare your practices against relevant standards like Privacy Act requirements and industry frameworks
- Prioritise gaps based on risk severity, regulatory requirements, and implementation feasibility
- Implement foundational controls like multi-factor authentication, encryption, and access management
- Establish incident response procedures detailing detection, containment, and notification steps
- Train staff on security awareness, data handling obligations, and incident reporting processes
- Schedule regular assessments and control testing to verify ongoing effectiveness
Comparison of popular compliance tools and MSP services helps you select appropriate solutions:
| Solution Type | Best For | Typical Cost | Key Advantage |
|---|---|---|---|
| Automated assessment tools | Initial gap analysis | $500-$2000 annually | Quick baseline establishment |
| Managed security services | Ongoing monitoring | $1000-$5000 monthly | 24/7 threat detection |
| Compliance consultants | Complex implementations | $150-$300 hourly | Specialised expertise |
| Integrated MSP packages | Comprehensive needs | $2000-$8000 monthly | Single vendor simplicity |
Staff training and ongoing assessments form the backbone of sustainable compliance. Technology alone cannot protect your business when employees fall for phishing emails or mishandle sensitive data. Quarterly security awareness sessions keep threats top-of-mind and reinforce proper procedures. Annual assessments verify that controls remain effective as your business evolves and threats change.
Maintaining compliance amid evolving risks requires adaptive strategies. Subscribe to security bulletins from OAIC and industry associations. Review and update policies annually or when significant business changes occur. Test incident response procedures through tabletop exercises. Monitor regulatory developments affecting your industry. Business data protection workflows should evolve continuously rather than remaining static documents.
Pro Tip: Create a compliance calendar tracking assessment dates, training schedules, policy reviews, and regulatory deadlines. This simple tool prevents oversights and demonstrates due diligence during audits. Include quarterly check-ins with your MSP or IT team to discuss emerging threats and control effectiveness.
Protecting sensitive data requires layered defences combining technology, processes, and people. Encryption protects data at rest and in transit. Access controls limit exposure to authorised personnel only. Monitoring systems detect unusual activity patterns. Backup procedures enable recovery from ransomware or disasters. Each layer compensates for others’ weaknesses, creating resilient protection.
Queensland SMBs face unique compliance considerations. State-based privacy laws, industry-specific regulations, and client contractual requirements create complex obligation matrices. Healthcare providers must satisfy NDIS requirements. Legal firms face Law Society practice standards. Financial services encounter ASIC oversight. Understanding your specific compliance landscape prevents costly oversights and positions you as a trusted service provider.
The rising cost of non-compliance makes proactive investment worthwhile. Breach notification expenses, regulatory fines, legal fees, and reputation damage far exceed prevention costs. A single significant breach can devastate an SMB financially and operationally. Investing in proper IT compliance transforms from optional expense to essential business protection.
How IT Start can support your SMB’s compliance journey
Navigating IT compliance complexities requires expertise, tools, and ongoing vigilance that challenge resource-constrained Brisbane businesses. IT Start delivers comprehensive compliance support through our specialised cyber security services, proactive business IT support, and secure cloud services. Our team understands Queensland’s regulatory environment and Brisbane’s business landscape, enabling us to deliver locally relevant solutions meeting global standards.
We assess your current compliance posture, identify gaps, and implement practical controls matching your risk profile and budget. Our managed services provide continuous monitoring, threat detection, and incident response capabilities without requiring you to hire full-time security specialists. We handle the technical complexity while you focus on growing your business, confident that compliance obligations are professionally managed.
Our SMB 1001 Gold certification demonstrates our commitment to industry-leading standards and transparency. We don’t just advise on compliance but model it through our own operations. This alignment ensures we understand the practical challenges you face and deliver solutions that actually work in real-world Brisbane business environments. Partner with IT Start to transform IT compliance from overwhelming burden to competitive advantage.
FAQ
What is the role of IT in compliance for small businesses?
IT provides the frameworks, technology, and policies that keep businesses compliant with privacy laws, industry regulations, and contractual obligations. This includes implementing security controls, monitoring systems for threats, managing data access, and documenting procedures for audits. IT teams translate legal requirements into technical safeguards that protect customer information and business operations.
How can Queensland SMBs align with the IS18 policy?
Implement security policies reflecting IS18’s core principles: protect sensitive information, enhance trust through transparency, and build resilience against disruptions. Focus on access controls, incident response capabilities, regular assessments, and staff training. While IS18 directly applies to government entities, adopting its standards positions your business for government contracts and demonstrates security maturity to private clients.
Why is IT compliance increasingly critical for Brisbane businesses?
Data breaches affecting Australian organisations increased 25% recently, with attackers specifically targeting SMBs lacking robust defences. Stricter privacy laws, client contractual requirements, and industry regulations create expanding compliance obligations. Non-compliance risks include regulatory fines, legal liability, reputation damage, and lost business opportunities. Proactive IT compliance protects your business and becomes a competitive differentiator.
What are managed IT services and how do they support compliance?
Managed service providers deliver security monitoring, threat detection, system updates, and expert guidance through subscription-based agreements. They provide access to enterprise-grade security tools, trained specialists, and collective intelligence about emerging threats. MSPs handle technical compliance complexities, freeing you to focus on core business activities while maintaining robust security postures that satisfy regulatory and client requirements.
How can SMBs stay updated on IT compliance requirements?
Subscribe to updates from the Office of the Australian Information Commissioner and relevant industry associations. Engage with MSPs who monitor regulatory changes and update client protections proactively. Attend quarterly training sessions covering emerging threats and evolving obligations. Review compliance requirements annually with legal and IT advisors. Join Brisbane business networks where peers share compliance experiences and solutions.

