Queensland small businesses face a critical dilemma: knowing which cybersecurity skills to prioritise when time and resources are limited. With 68% of Australian SMEs experiencing cyberattacks, choosing the right learning path isn’t optional. This guide provides a practical roadmap tailored to Queensland SME needs, helping you focus on cybersecurity knowledge that delivers real protection without overwhelming your schedule or budget.
Table of Contents
- Selection Criteria For Cyber Security Learning Priorities For SME Owners
- Understanding The Cyber Security Threat Landscape For Queensland SMEs
- Critical Cyber Security Skills And Knowledge For Small Business Owners
- Essential Cyber Security Training And Learning Resources For SMEs
- Regulatory And Compliance Knowledge For Queensland Small Businesses
- Key Cyber Security Areas To Learn For SMEs Using Cloud Solutions
- Evaluating Learning Paths: DIY Vs Managed Cyber Security Support For SMEs
- Leveraging Local Resources And Support For Cyber Security Learning In Queensland
- Summary Comparison And Situational Recommendations
- Find The Right Cyber Security Support With IT Start
Key takeaways
| Point | Details |
|---|---|
| Prioritise by risk | Focus cybersecurity learning on threats most likely to impact your business, including phishing and ransomware. |
| Master foundational skills | Phishing recognition, password hygiene, and multi-factor authentication form your essential defence layer. |
| Understand compliance obligations | Meet Australian regulatory requirements like the Notifiable Data Breaches scheme to avoid penalties and reputational damage. |
| Address cloud security | With 70% of SMEs using cloud services, learn identity management and configuration best practices to protect cloud assets. |
| Evaluate learning approaches | Compare self-directed learning against managed security services based on your resources, expertise, and risk tolerance. |
Selection criteria for cyber security learning priorities for SME owners
Many Queensland SMEs underestimate their internal cybersecurity knowledge gap. 40% of Australian SMEs lack internal cybersecurity knowledge, leaving them vulnerable to evolving threats. Without a clear framework, business owners waste time on irrelevant topics whilst critical vulnerabilities remain unaddressed.
A practical three-tier model helps you prioritise effectively. Start with risk awareness to understand your threat landscape. Build practical skills that directly defend against common attacks. Finally, ensure regulatory compliance to avoid legal penalties and customer trust erosion.
Your business size and sector significantly influence learning urgency. A healthcare practice handling patient data faces different compliance pressures than a retail shop. Manufacturing firms may prioritise operational technology security, whilst professional services focus on data protection. Assess your specific risk profile before committing time to training.
Cost and resource availability shape feasible learning paths. Solo operators need quick, focused training on high-impact topics. Larger SMEs with small teams can distribute learning responsibilities across staff members. Budget constraints may push you towards free government resources or justify investment in managed services that deliver expertise without the learning curve.
Pro Tip: Document your top three business-critical systems or data types, then prioritise learning topics that protect these assets first. This targeted approach maximises return on your training investment.
Understanding the cyber security threat landscape for Queensland SMEs
Australian small businesses operate in a hostile digital environment. The 68% of Australian SMEs experiencing cyberattacks statistic isn’t abstract fear-mongering. It reflects daily reality for Queensland businesses across every sector. Attackers specifically target smaller organisations, knowing they often lack dedicated security staff.
Phishing remains the dominant attack vector you must prioritise. Phishing represents over 35% of incidents targeting Australian SMEs, making it the single most important threat to understand. These attacks arrive via email, SMS, or social media, tricking staff into revealing credentials or transferring funds. A single successful phishing attack can compromise your entire network.
Emerging threats demand your attention beyond traditional phishing:
- Ransomware attacks encrypt business-critical files, demanding payment for restoration
- Business email compromise schemes impersonate executives to authorise fraudulent payments
- Social engineering exploits human psychology rather than technical vulnerabilities
- Supply chain attacks compromise trusted vendors to access customer networks
Understanding these cyber security threats Brisbane SMEs face helps you allocate learning time wisely. Focus on recognition skills for the attacks most likely to hit your business, not theoretical knowledge about sophisticated nation-state tactics irrelevant to your risk profile.
“The average cost of a cyberattack on an Australian SME exceeds $39,000, but prevention through education costs a fraction of that amount. Knowledge is your most cost-effective defence layer.”
Critical cyber security skills and knowledge for small business owners
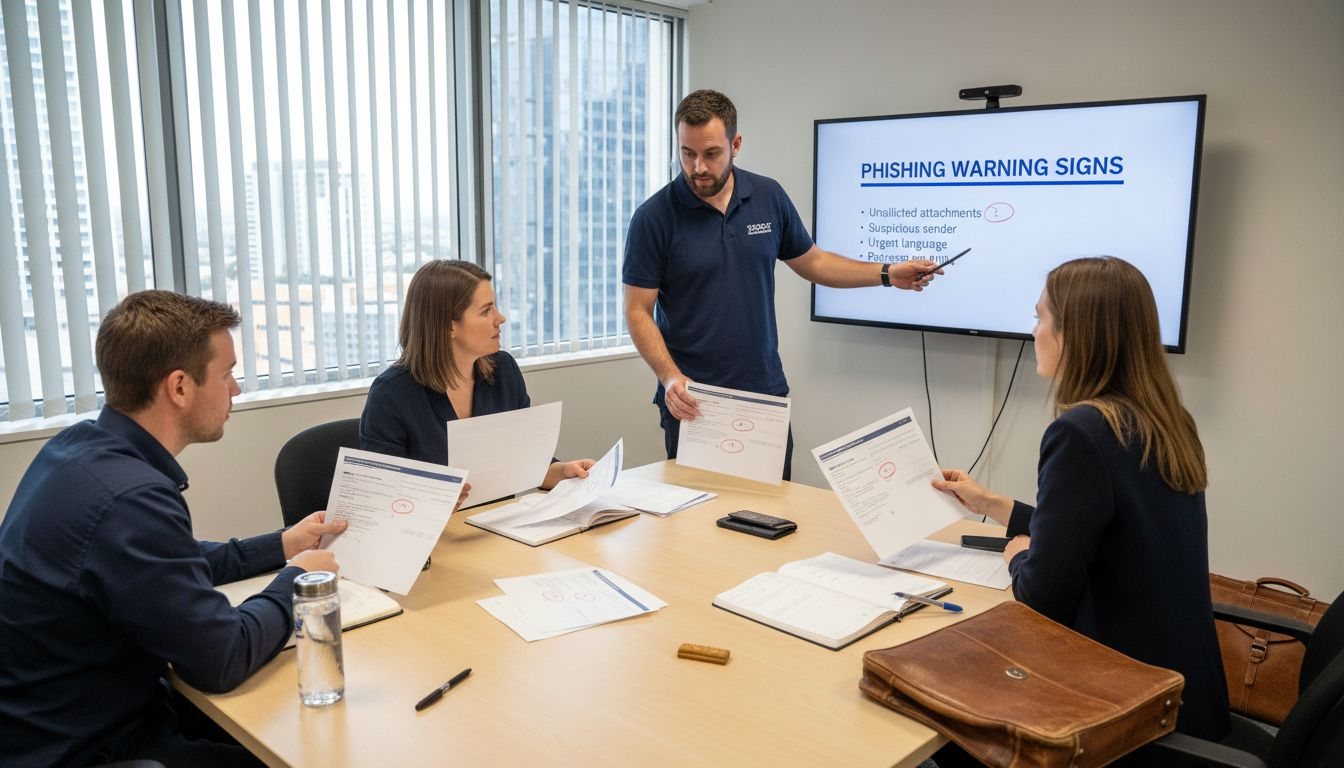
Recognising and preventing phishing attempts forms your foundational defence. Train yourself and staff to identify suspicious sender addresses, urgent language designed to bypass critical thinking, and requests for sensitive information. Simulated phishing training reduces susceptibility by 45%, making it one of the highest-value skills you can develop.
Implementing strong password hygiene and multi-factor authentication protects accounts when credentials leak. Use unique passwords for every service, minimum 12 characters combining letters, numbers, and symbols. Password managers eliminate the memory burden whilst strengthening security. Multi-factor authentication adds a second verification step, blocking 99% of automated attacks even when passwords are compromised.
Understanding network security and endpoint protection basics helps you make informed decisions about business systems. Learn how firewalls filter malicious traffic, why regular software updates close security holes, and what antivirus software can and cannot detect. This knowledge empowers you to evaluate vendor security claims and identify gaps in your current setup.
Additional essential skills include:
- Recognising social engineering tactics across phone, email, and in-person interactions
- Implementing secure backup procedures with offline or cloud-based redundancy
- Understanding basic access controls to limit who can view or modify sensitive data
- Developing incident response awareness so you know immediate steps when breaches occur
These cyber security essentials Queensland SMEs need aren’t highly technical. They require awareness, consistent habits, and organisational discipline more than deep technical expertise. Focus on building reliable processes that your entire team can follow consistently.
Pro Tip: Schedule monthly 10-minute security discussions with your team to review recent phishing attempts or security news. Regular exposure builds intuitive threat recognition better than annual training sessions.
Essential cyber security training and learning resources for SMEs
Australian cybersecurity training programs suitable for SMEs span free government initiatives to paid professional courses. The Australian Cyber Security Centre offers free online modules covering threat awareness and protective measures. State government programs provide workshops tailored to local business needs. Industry associations often negotiate member discounts for accredited training providers.
Ongoing staff training and awareness programmes deliver better protection than one-time sessions. Phishing simulation training reduces phishing susceptibility by 45% when conducted regularly. Monthly micro-learning sessions maintain awareness without disrupting productivity. Annual comprehensive training provides depth whilst regular reinforcement ensures retention.
Training formats accommodate different learning preferences and operational constraints:
| Format | Advantages | Limitations | Best For |
|---|---|---|---|
| Online modules | Self-paced, cost-effective, accessible anytime | Lacks interaction, requires self-discipline | Solo operators, distributed teams |
| In-person workshops | Interactive, immediate Q&A, networking opportunities | Higher cost, requires travel time | Teams wanting collaborative learning |
| Simulated phishing | Realistic practice, identifies vulnerable staff | Requires ongoing subscription | Organisations prioritising email security |
| Certification programs | Formal credentials, comprehensive coverage | Significant time and cost investment | Businesses requiring compliance evidence |
Evaluate cyber security training options based on your team size, budget, and learning objectives. Small teams benefit from focused online modules addressing specific threats. Larger organisations justify investment in comprehensive programs with ongoing support and updates.
Free resources provide solid foundations:
- ACSC Essential Eight guidance for baseline security measures
- OAIC privacy training modules for data handling compliance
- Industry-specific security frameworks from professional associations
Regulatory and compliance knowledge for Queensland small businesses
Mandatory reporting under the Notifiable Data Breaches scheme requires SMEs handling customer data to notify affected individuals and the Office of the Australian Information Commissioner when eligible breaches occur. Eligible breaches involve unauthorised access or disclosure likely to result in serious harm. Failing to report within 30 days triggers penalties and reputational damage.
Australian Privacy Principles govern how businesses collect, use, and secure personal information. You must only collect information necessary for business functions, protect it with reasonable security measures, and allow individuals to access their data upon request. These principles apply to businesses with annual turnover exceeding $3 million or those trading in personal information.
Consequences of non-compliance extend beyond financial penalties. The OAIC can impose fines up to $2.5 million for serious or repeated privacy breaches. More damaging is customer trust erosion following publicised incidents. Queensland SMEs operating in competitive markets cannot afford reputational harm from preventable compliance failures.
Key regulatory obligations include:
- Conducting regular privacy impact assessments for new data collection initiatives
- Maintaining accurate records of data holdings and security measures implemented
- Developing clear privacy policies accessible to customers and staff
- Implementing breach response procedures before incidents occur
- Training staff on privacy obligations relevant to their roles
Understanding regulatory compliance Queensland SMEs require isn’t optional. It’s a fundamental business risk management responsibility that protects both customers and your organisation from legal and financial consequences.
Key cyber security areas to learn for SMEs using cloud solutions
Cloud adoption transforms SME operations, with 70% of SMEs using cloud services for email, file storage, and business applications. This shift demands new security knowledge focused on identity management and access controls rather than traditional network perimeter defence.
Identity access management and multi-factor authentication form your primary cloud security layer. Cloud services rely on credentials for access control, making strong authentication critical. Implement MFA across all cloud accounts, especially those with administrative privileges. Use conditional access policies that restrict logins based on location, device, or risk level.
Misconfigured cloud security settings create the majority of cloud breaches. Default configurations often prioritise convenience over security, leaving data publicly accessible or inadequately encrypted. Learn to review sharing permissions, encryption settings, and access logs regularly. Understand your cloud provider’s shared responsibility model, which defines where their security obligations end and yours begin.
Best practices for safeguarding cloud assets:
- Enable encryption at rest and in transit for sensitive data
- Implement least-privilege access so users only access necessary resources
- Monitor access logs for unusual activity patterns indicating compromised accounts
- Maintain offline backups independent of your primary cloud provider
- Review third-party app permissions that access your cloud data
| Cloud Security Area | Priority Level | Learning Time Required | Impact on Risk Reduction |
|---|---|---|---|
| Multi-factor authentication | Critical | 2 hours | Very High |
| Access permission review | High | 4 hours | High |
| Encryption configuration | High | 3 hours | High |
| Backup procedures | Critical | 3 hours | Very High |
| Log monitoring | Medium | 5 hours | Medium |
Explore cloud computing security benefits and cloud data security Brisbane resources to deepen your understanding of protecting cloud-based business operations.
Pro Tip: Conduct quarterly access reviews where you audit who has access to cloud resources and revoke unnecessary permissions. This simple practice dramatically reduces your attack surface.
Evaluating learning paths: DIY vs managed cyber security support for SMEs
Self-directed cybersecurity learning offers cost advantages and builds internal capability. You control the pace and focus areas, tailoring education to specific business needs. Free resources reduce financial barriers, making this approach accessible to bootstrapped startups. However, DIY learning demands significant time investment, struggles with knowledge gaps you don’t recognise, and lacks ongoing support when threats evolve.
Managed cybersecurity services provide immediate access to specialist expertise without the learning curve. Managed services offer 40% faster incident response compared to internal teams, reducing breach impact and recovery costs. Providers monitor threats continuously, implement best-practice controls, and handle compliance requirements. This approach frees your time for core business activities whilst ensuring professional-grade protection.
| Aspect | DIY Learning | Managed Services |
|---|---|---|
| Initial cost | Low to moderate | Moderate to high |
| Time investment | High (ongoing) | Low (delegation) |
| Expertise depth | Variable, gaps likely | Professional, comprehensive |
| Response speed | Slow, learning required | Fast, immediate expertise |
| Scalability | Difficult as complexity grows | Easy, provider scales resources |
| Compliance support | Self-managed, risk of errors | Included, professional guidance |
Cost and resource considerations shape your optimal path. Businesses with under 10 staff often lack bandwidth for comprehensive DIY security whilst managing operations. Moderate-sized SMEs might hybrid approaches, handling basic security whilst outsourcing complex areas like threat monitoring or compliance audits. Budget-constrained startups may bootstrap initially but should plan transitions to managed services as revenue grows.
Factors favouring DIY learning:
- Limited budget with time available for self-education
- Simple IT environment with few cloud services or connected systems
- Technical background amongst ownership or staff
- Desire to build internal security culture and awareness
Factors favouring managed services:
- Limited time to dedicate to security learning and implementation
- Complex IT environment requiring specialist knowledge
- Regulatory compliance requirements demanding documentation and audits
- High-value data or systems where breach costs exceed service fees
Explore managed security services benefits to understand how professional support accelerates protection whilst reducing owner workload.
Leveraging local resources and support for cyber security learning in Queensland
Queensland-specific cybersecurity workshops and certification programmes address regional business needs more effectively than generic national training. Queensland-specific cybersecurity resources increase effective uptake by 20% because they incorporate local regulatory context, industry examples, and networking opportunities with nearby businesses facing similar challenges.
Local expertise brings practical advantages. Brisbane-based security providers understand Queensland SME operating environments, common technology stacks, and sector-specific risks. They offer face-to-face consultations, rapid on-site response when incidents occur, and relationships with local law enforcement for serious breaches. This proximity builds trust and enables ongoing support relationships that remote providers struggle to match.
Free security assessments from local providers identify gaps in your current protection without financial commitment. These assessments benchmark your security posture against industry standards, prioritise remediation efforts, and provide roadmaps for improvement. Even if you pursue DIY learning, professional assessment ensures you focus on actual vulnerabilities rather than perceived risks.
Available local resources include:
- Queensland government small business cybersecurity grants and subsidised training
- Brisbane industry association workshops on sector-specific security challenges
- Local university continuing education programmes offering practical security courses
- Regional managed service providers offering free initial consultations and assessments
Access business IT support services that combine local knowledge with professional security expertise. Local support improves practical cybersecurity adoption by reducing implementation friction and providing ongoing assistance as your business and threats evolve.
Summary comparison and situational recommendations
Choosing the right cybersecurity learning path depends on your specific SME profile, resources, and risk exposure. This comparison synthesises training options and matches them to common Queensland SME situations.
| SME Profile | Priority Learning Areas | Recommended Approach | Estimated Time Investment |
|---|---|---|---|
| New startup, under 5 staff | Phishing awareness, password hygiene, cloud basics | Free online modules plus MFA implementation | 10 hours initial, 2 hours monthly |
| Established SME, 5-20 staff | All foundational skills plus compliance and incident response | Paid training programme plus simulated phishing | 20 hours initial, 4 hours monthly |
| Cloud-heavy operations | Identity management, cloud configuration, backup procedures | Specialist cloud security training or managed services | 15 hours initial, 3 hours monthly |
| Regulated industries | Compliance requirements, data protection, audit readiness | Comprehensive certification plus managed compliance support | 30 hours initial, 6 hours monthly |
Risk profiles should drive learning priorities. High-risk scenarios include handling sensitive customer data, processing financial transactions, or operating in targeted industries like healthcare or legal services. These businesses benefit from accelerated learning or immediate managed service engagement. Lower-risk operations can adopt gradual learning approaches, building capabilities over time as resources permit.
Situational recommendations:
- Solo operators with technical background should pursue self-directed learning focused on high-impact basics like MFA and phishing recognition
- Growing teams should implement formal training programmes with regular reinforcement and accountability measures
- Businesses experiencing rapid growth should engage managed services before security gaps create vulnerabilities
- SMEs with compliance obligations should prioritise regulatory knowledge and documentation practices early
Review the complete cyber security guide Queensland SMEs for deeper exploration of protection strategies tailored to your business stage and sector.
Find the right cyber security support with IT Start
Navigating cybersecurity learning whilst running your Queensland business demands time you may not have. IT Start delivers comprehensive cybersecurity and IT support tailored specifically for Queensland SMEs, implementing the protection strategies outlined in this guide without requiring you to become a security expert.
Our cyber security services cover threat monitoring, incident response, compliance management, and staff training aligned with your business risk profile. We handle technical complexities whilst you focus on business growth. Expert support reduces risks and frees resources that DIY approaches consume.
IT Start’s business IT support and cloud services solutions integrate security into every aspect of your technology environment. From initial assessments identifying vulnerabilities to ongoing managed protection, we provide the expertise Queensland SMEs need to operate confidently in an increasingly hostile digital landscape.
Frequently asked questions
What basic cyber security skills should I learn as a small business owner?
Focus on phishing recognition as your highest-priority skill, since it defends against over 35% of attacks targeting Australian SMEs. Master password hygiene including unique passwords per service and multi-factor authentication implementation. Understanding basic network security concepts and endpoint protection helps you make informed decisions about business systems. These cyber security essentials Queensland businesses need deliver maximum protection relative to learning time invested.
How can I ensure my small business meets Australian cyber security compliance requirements?
Understand the Notifiable Data Breaches scheme requires timely reporting of eligible breaches involving unauthorised access likely to cause serious harm. Learn Australian Privacy Principles governing data collection, use, and protection relevant to your business operations. Maintain accurate records of your data holdings, security measures implemented, and staff training completed. Develop breach response procedures before incidents occur so you can act quickly when required. Regular compliance for Queensland SMEs reviews ensure you stay current as regulations evolve.
Should I manage cyber security myself or hire a service?
DIY learning saves costs but requires significant ongoing time investment and risks knowledge gaps you don’t recognise. Managed services provide 40% faster incident response and professional expertise without the learning curve, making them cost-effective for businesses valuing time and certainty. Evaluate based on your available time, technical background, IT environment complexity, and breach risk tolerance. Many SMEs benefit from hybrid approaches, handling basic security whilst outsourcing complex areas like threat monitoring. Review managed security services benefits to determine if professional support suits your situation.
How much time should I dedicate to cyber security learning?
New businesses should invest approximately 10 hours initially covering phishing awareness, password hygiene, and MFA implementation, then maintain 2 hours monthly for updates and reinforcement. Established SMEs with teams need 20 hours initial training plus 4 hours monthly for ongoing awareness. Cloud-heavy operations require 15 hours focused on identity management and configuration, plus 3 hours monthly maintenance. Regulated industries demand 30 hours comprehensive learning covering compliance obligations plus 6 hours monthly to stay current. Adjust based on your risk profile and whether you pursue self-directed learning or supplement with managed services.