TL;DR:
- Nearly 25% of cyber insurance claims in 2024 were rejected due to coverage failures, leaving SMBs vulnerable. Understanding policy details, regulatory obligations, and infrastructure controls is essential to activate and maintain effective cyber protection. A strong security foundation aligned with insurance requirements prevents claims denial and enhances overall cyber resilience.
Nearly one in four cyber insurance claims filed in 2024 were rejected for failing to meet coverage requirements. For Queensland small and medium-sized businesses, that statistic is confronting, especially when most owners assume their policy will simply pay out after an incident. Cyber liability insurance is one of the most misunderstood financial tools available to SMBs, often purchased without a clear understanding of what triggers a valid claim, what the policy excludes, and how it connects to Australia’s growing web of regulatory obligations. This guide cuts through the confusion and gives you a practical framework for understanding, choosing, and activating cyber liability insurance as a genuine business protection tool.
Table of Contents
- What cyber liability insurance actually covers
- The connection between insurance and compliance duties
- Common exclusions and why claims get denied
- How cyber insurance drives better security in your business
- Why compliance is only half the story for Queensland SMBs
- Protect your business with expert cyber resilience support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Understand policy coverage | Know what your cyber liability insurance actually pays for, including both direct and third-party costs. |
| Align with compliance rules | Coordinate insurance notifications with legal requirements, especially for data breach and ransomware events. |
| Avoid common exclusions | Claims can be denied if you miss disclosure or fail to maintain IT security controls—read the fine print closely. |
| Insurance boosts cyber maturity | Treat each insurance renewal as a chance to upgrade your cyber defences, not just renew paperwork. |
| Prevention still matters most | No insurance replaces the need for robust security practices and a well-prepared incident response plan. |
What cyber liability insurance actually covers
Before you can make a smart decision about cyber liability insurance, you need to know exactly what you’re buying. Most policies divide coverage into two broad categories: first-party losses and third-party liabilities.
First-party losses are the direct costs your business incurs when a cyber incident hits you. These include forensic investigation to find out how the breach happened, data recovery costs, business interruption losses while your systems are offline, ransomware payment consultancy, and notification expenses when you’re legally required to tell affected customers about a data breach.
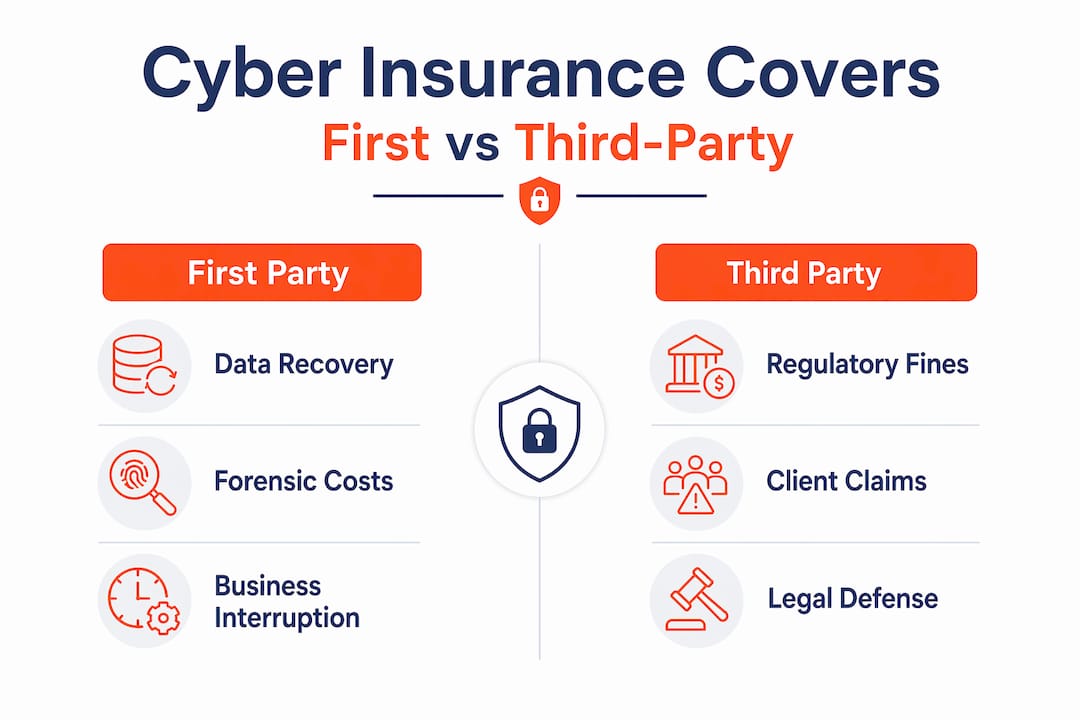
Third-party liabilities are the costs that arise when someone external, such as a client or regulatory body, suffers harm as a result of an incident on your network. These include legal defence costs, settlements, regulatory fines, and civil claims from affected parties.
Cyber liability insurance is designed to help businesses financially recover from cyber incidents by funding first-party response costs and, depending on the policy, third-party liabilities. The key phrase there is “depending on the policy.” Not every cyber insurance product is created equal, and the gap between a comprehensive policy and a bare-bones one can be significant.
Here’s a practical comparison of what different policy tiers typically cover:
| Coverage category | Basic policy | Comprehensive policy |
|---|---|---|
| Breach investigation costs | Yes | Yes |
| Customer notification expenses | Yes | Yes |
| Business interruption losses | Partial | Full, including dependent systems |
| Legal defence costs | Limited | Broad, including regulatory defence |
| Regulatory fines | Rarely | Often included, subject to limits |
| Ransomware negotiation support | No | Yes, with specialist access |
| Reputational management costs | No | Yes |
| Social engineering fraud | No | Often included |
Common costs covered under most mid-tier policies include:
- Hiring a forensic IT firm to investigate how the breach occurred
- Notifying customers and regulators within required timeframes
- Credit monitoring services for affected individuals
- Crisis communications and public relations management
- Lost revenue from system downtime
- Restoring corrupted or encrypted data
Pro Tip: When comparing policies, ask your broker specifically whether dependent business interruption is covered. This applies when your systems go down because a third-party supplier or cloud platform is breached, not your own network. Many SMBs are surprised to find this isn’t standard.
The connection between insurance and compliance duties
Understanding what your policy covers is only part of the picture. The harder challenge for Queensland SMBs is aligning that coverage with Australia’s expanding regulatory landscape around cyber incidents.

Cyber liability insurance intersects with regulatory and statutory incident-response obligations, including ransomware payment reporting under the Cyber Security Act 2024. This is a significant development that many Queensland business owners are still catching up with.
Here is what the Act means in plain terms: if your business makes a ransom payment to resolve a cyber extortion attack, you must report that payment to the Australian Signals Directorate within 72 hours. This obligation exists regardless of whether you have insurance. Your insurer will also have their own notification requirements under your policy terms. That means, in a ransomware scenario, you may need to simultaneously notify:
| Reporting obligation | Recipient | Timeframe |
|---|---|---|
| Ransomware payment report | Australian Signals Directorate | Within 72 hours of payment |
| Insurer incident notification | Your cyber insurer | As per policy terms (often 24 to 72 hours) |
| Privacy Act notifiable breach | OAIC if applicable | As soon as practicable |
| Client contractual obligations | Affected customers | As per contract terms |
“Businesses that fail to coordinate their internal incident response with both their insurer’s notification requirements and statutory obligations risk double jeopardy: a denied claim and legal exposure.” This is a real scenario playing out in the Australian market right now.
The practical implication is that you cannot afford to treat insurance and regulatory compliance as separate streams. They must be part of a single, integrated incident response plan. Your team needs to know, before an attack occurs, who calls the insurer, who contacts the ASD, and who manages data protection notifications. Businesses that have well-documented privacy policies and clear internal procedures are far better positioned to meet every deadline without losing coverage.
One underappreciated detail: many insurers require you to use their approved incident response vendors during a claim. If you hire your own forensics firm before notifying the insurer, they may decline to cover that cost. Read your policy before an incident happens, not during one.
Common exclusions and why claims get denied
Even businesses that think they’re well covered can find their claims rejected. Claim denials rarely happen by accident. They almost always trace back to specific exclusions in the policy or a failure to meet conditions that the insured either didn’t know about or didn’t take seriously.
Cyber insurance coverage commonly hinges on how policies define “insurable events” and on exclusions such as prior-known vulnerabilities, failure to notify the insurer promptly, poor security hygiene, and other conditions. Let’s break these down into practical terms.
The most common exclusions that catch Queensland SMBs off guard include:
- Known vulnerabilities not remediated: If your IT systems had a documented flaw that was never patched, and a breach exploited that flaw, the insurer may argue you knew about the risk and failed to act.
- Failure to meet minimum security standards: Many policies require you to maintain specific controls like multi-factor authentication (MFA), regular backups, and endpoint protection. If those controls weren’t in place when the incident occurred, the claim can be denied.
- Late notification to the insurer: Policies typically require you to report a suspected incident within a defined window, sometimes as little as 24 hours. Waiting until the forensic investigation is complete often violates this clause.
- Incidents predating the policy: If a breach began before your policy commenced but wasn’t discovered until after, the insurer may argue the “trigger event” falls outside the coverage period.
- Employee dishonesty or insider threats: Some policies exclude losses caused by deliberate internal actions, which requires separate fidelity cover.
- War and state-sponsored attacks: A growing exclusion across the market, this is particularly relevant given the rise of nation-state cyber activity targeting Australian infrastructure.
Maintaining solid cybersecurity policies is not just good IT governance; it’s a prerequisite for your insurance to function. Addressing common vulnerabilities before renewing your policy is essential to avoid gaps that insurers will exploit to deny claims.
Pro Tip: Ask your insurer for a written list of the minimum security controls required to maintain your coverage. Then document your compliance with each one, and update that documentation at every renewal. If a claim is disputed, that paper trail is your strongest defence.
How cyber insurance drives better security in your business
Here’s a perspective shift that many Queensland SMB owners don’t expect: cyber liability insurance isn’t just a financial safety net. Used properly, it actively strengthens your security posture.
Cyber liability insurance can be leveraged by industry bodies as a tool to improve SMB cyber resilience, using touchpoints like renewals to deliver consistent cyber security messaging. The renewal process in particular is an underused opportunity.
Here’s a step-by-step approach to using the insurance cycle as a security improvement engine:
- Map your digital assets before renewal. Before your policy renews, conduct an audit of all systems, data types, and third-party integrations your business depends on. This gives you an accurate risk picture and ensures your coverage limits reflect your actual exposure.
- Review and implement required controls. Use your insurer’s minimum control requirements as a checklist. Common requirements include MFA, endpoint detection software, encrypted backups stored off-site, and staff security awareness training.
- Document your incident response plan. Insurers look favourably on businesses that have a written, tested response plan. This includes who does what during an incident, how you notify the insurer, and how you preserve evidence.
- Brief key staff on obligations. Your financial controller, IT manager, and operations lead all need to understand their role in a cyber event. A well-rehearsed response reduces the risk of procedural mistakes that void coverage.
- Benchmark your premiums. As your security posture improves, use that evidence to negotiate better premium terms. Insurers price risk, and demonstrable controls reduce your risk profile.
Strong cybersecurity practices don’t just reduce the likelihood of an incident; they directly influence your insurability and your premium cost. Businesses that treat insurance as a passive product miss this compounding benefit.
For Queensland SMBs seeking practical guidance on building that internal capability, the connection between security investment and insurance value is one of the most compelling business cases available.
Why compliance is only half the story for Queensland SMBs
Here’s the uncomfortable truth we see consistently in the Queensland market: most SMBs that face denied claims weren’t negligent in the way you might expect. They had insurance. They thought they were compliant. What they lacked was a genuine governance mindset around cyber risk.
Buying a cyber liability policy is relatively easy. Building the internal discipline to keep that policy active and claimable is where most businesses fall short. Insurers price risk tightly and the availability of loss data is shaping underwriting requirements that are only getting stricter. SMBs that treat policy purchase as the finish line will increasingly find themselves uninsured when it matters most.
The cybersecurity trends affecting Queensland SMBs in 2025 and 2026 point to an environment where insurers are demanding more evidence of security maturity, not less. The days of ticking a box on an application form and assuming you’re covered are effectively over.
What does a governance mindset actually look like in practice? It means treating your security controls, your incident response plan, your staff training records, and your insurer notifications as a living workflow, not a set-and-forget arrangement. It means reviewing your risk position at least annually, not only when the renewal notice arrives. And it means understanding that insurance is the last line of financial defence, not the first.
The businesses that activate claims successfully are almost always those that invested in prevention first. Insurance works best when it’s covering genuinely unforeseeable events, not plugging gaps left by avoided IT spend. If your IT environment has known weaknesses, an insurance policy won’t fix them. It will simply decline to pay when they’re exploited.
Our view at IT Start is that the strongest insurance strategy for any Queensland SMB is one where the claim never needs to be made, because the security foundation is solid enough to stop most incidents before they become crises.
Protect your business with expert cyber resilience support
Understanding cyber liability insurance is the first step. Putting it into practice requires the right IT foundation beneath it. At IT Start, we work with Queensland SMBs to build the security controls, documentation, and incident response processes that keep your coverage valid and your business protected. Our cyber security services are designed specifically for businesses that need enterprise-grade protection without enterprise-scale overhead. Whether you’re managing sensitive client data in professional services, healthcare, or financial services, we help you stay compliant and insurable. Our secure cloud solutions and managed IT support provide the proactive infrastructure that insurers expect to see. Reach out for a free assessment and find out where your gaps are before your insurer does.
Frequently asked questions
What is typically excluded from cyber liability insurance policies?
Policies often exclude claims from known but undisclosed incidents, outdated security controls, or late reporting to the insurer. Common exclusion themes include insufficient IT security systems and failure to provide timely notice of a suspected incident.
How quickly must Queensland businesses report ransomware payments?
You must report to the Australian Signals Directorate within 72 hours after payment, as required by the Cyber Security Act 2024. This reporting obligation applies regardless of whether your insurer is notified separately.
Can failing basic security controls cause claims to be denied?
Yes. Insurers commonly deny claims when controls like MFA or verified backups are not properly implemented and maintained at the time of the incident. You may need to provide evidence of control compliance as part of the claims process.
Is cyber insurance required by law for Queensland SMBs?
No, cyber liability insurance is not a legal requirement for Queensland businesses. However, it strongly supports your ability to manage financial risk and meet regulatory compliance obligations under Australian law.
How does cyber insurance help improve our cyber security?
Insurance touchpoints like onboarding and renewals prompt better security practices and documentation, which can reduce your risk profile and, over time, lower your premiums while improving your overall security posture.



