TL;DR:
- Many Queensland SMEs overlook the cost-effective benefits of adopting formal IT standards to improve security and operational efficiency. Implementing frameworks like ACSC Essential Eight and SMB1001 creates consistent, scalable processes that reduce risks and downtime. Starting small and building systematically with documented controls enhances resilience, compliance, and competitive advantage.
Most Queensland business owners assume IT standards are the domain of large corporations with dedicated compliance teams and deep pockets. That assumption is quietly costing SMEs real money. When your systems run on ad-hoc decisions and verbal agreements between staff, inefficiencies multiply and security gaps widen. The good news is that formal IT standards are far more accessible than they appear, and the businesses that adopt them early gain a genuine competitive edge. This guide explains what IT standards are, why they matter for businesses your size, and how to put them to work without overcomplicating things.
Table of Contents
- What are IT standards and why do they matter?
- How IT standards drive operational efficiency
- The role of IT standards in cybersecurity
- Choosing and implementing IT standards for your business
- What most Queensland SMEs get wrong about IT standards
- Need expert help with IT standards?
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Standards boost efficiency | IT standards streamline your processes, reduce errors, and help your business scale smoothly. |
| Critical for cybersecurity | Using IT standards is one of the most effective ways to guard against cyber threats and remain compliant. |
| Choose relevant frameworks | Select the standards best matched to your business sector and start small for sustainable improvement. |
| Long-term business resilience | Establishing standardised IT practices now builds your SME’s resilience and competitive edge in Queensland. |
What are IT standards and why do they matter?
IT standards are formally documented guidelines that define how technology should be implemented, managed, and secured within an organisation. Think of them as the rulebook that keeps your systems consistent, your team aligned, and your risks manageable. Without them, every IT decision becomes a judgment call, and judgment calls add up to chaos over time.
Several key frameworks are directly relevant to Queensland SMEs:
- ISO 27001: The international standard for information security management. It helps you identify risks to your data and build a systematic approach to protecting it.
- ITIL (Information Technology Infrastructure Library): A framework focused on delivering IT services effectively. It brings structure to everything from helpdesk requests to major system changes.
- COBIT (Control Objectives for Information and Related Technologies): A governance framework that aligns IT activities with broader business goals.
- ACSC Essential Eight: Developed by the Australian Cyber Security Centre, this is a prioritised list of mitigation strategies specifically tailored to the Australian threat environment.
- SMB1001: An Australian standard purpose-built for small and medium businesses. It provides a tiered, practical pathway to improving cybersecurity without requiring enterprise-level resources.
As formalised guidelines for implementing, managing, and securing technology, these standards ensure consistency, interoperability, and risk mitigation across your operations. That’s not corporate jargon. Consistency means your team handles IT the same way every time. Interoperability means your tools talk to each other properly. Risk mitigation means you’re less likely to face a breach, data loss, or a compliance fine.
“IT standards are not a destination. They are a discipline. The businesses that treat them as ongoing practice rather than a one-off project are the ones that stay resilient.”
For Queensland SMEs, the relevance is even sharper. Many industries operating in this state, including financial services, healthcare, legal, and professional services, face regulatory obligations that map directly to these standards. Following Brisbane IT compliance best practices is increasingly expected, not just recommended. A standard gives you a credible, defensible position if your practices are ever called into question.
How IT standards drive operational efficiency
With a clear understanding of what standards are, let’s see how they directly boost your operational efficiency. The connection is more direct than most business owners realise.
When your IT operations run on documented, repeatable processes, your team spends less time guessing and more time delivering. A staff member who knows exactly how to onboard a new employee’s laptop, configure access rights, and register a support ticket is far more productive than one improvising from memory each time. Standards create that documentation and enforce that consistency.

The efficiency gains are measurable. Standardised processes reduce errors, redundancies, and downtime, and they enable scalability for SMEs. Fewer errors mean fewer support calls. Less redundancy means lower software and hardware costs. Less downtime means your team stays productive rather than waiting for systems to come back online.
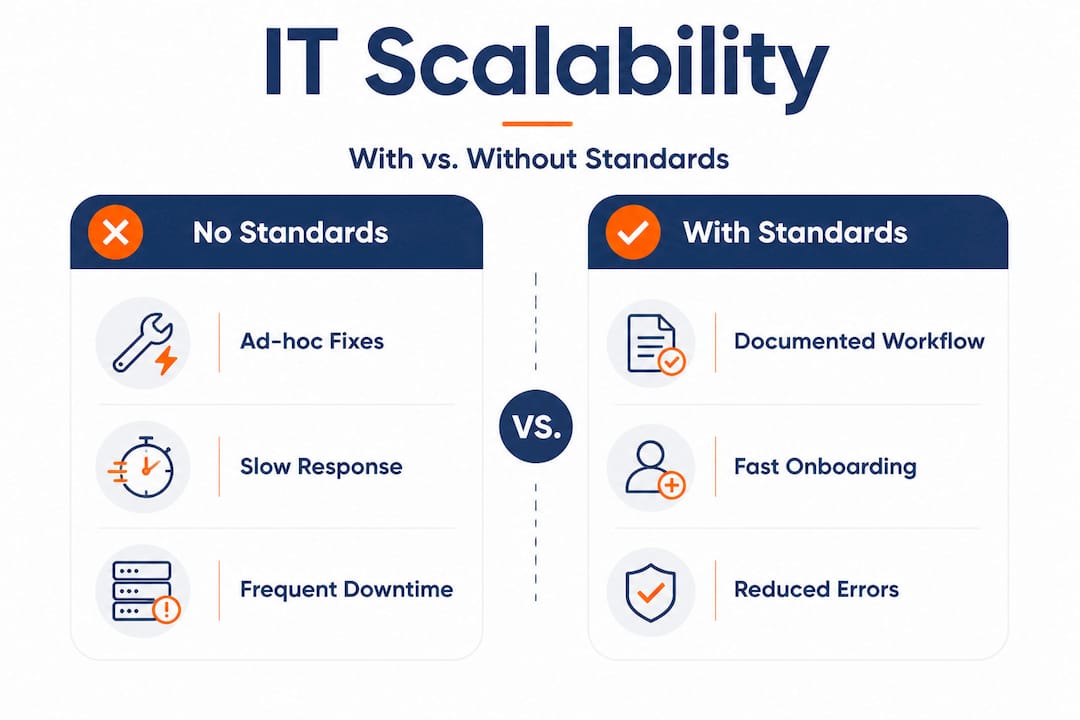
Here’s a practical comparison of what operations typically look like with and without IT standards:
| Area | Without IT standards | With IT standards |
|---|---|---|
| Incident response | Ad-hoc, inconsistent, slow | Structured, logged, resolved faster |
| Staff onboarding | Varies by manager, often incomplete | Consistent checklist, fully documented |
| Software updates | Done when remembered, if at all | Scheduled, automated, tracked |
| Data backup | Irregular or untested | Automated, verified, offsite copies |
| Vendor management | Based on personal preference | Evaluated against defined criteria |
| Scalability | Painful and expensive | Structured and repeatable |
Scalability is where standards pay off most visibly. When a Brisbane professional services firm grows from 10 to 30 staff, an IT environment built on standard protocols scales predictably. You add users to an established system rather than rebuilding from scratch each time. You can also leverage automation for process efficiency across your business more easily when your underlying IT is consistent and well-documented.
Pro Tip: If you want a quick win, start with your IT asset register. Documenting every device, its owner, operating system, and software creates immediate visibility and is the first step most standards require. It takes a day to set up and pays dividends for years.
Standards also reduce your maintenance burden over time. Businesses without clear processes tend to spend heavily on reactive fixes, emergency call-outs, and re-work. Businesses with documented IT standards spend on proactive maintenance, which costs considerably less. You can boost efficiency with IT compliance by treating your IT framework as infrastructure rather than overhead.
The role of IT standards in cybersecurity
Beyond efficiency, one of the most pressing needs for businesses is cybersecurity, an area where IT standards are indispensable. Cyber threats targeting Australian SMEs have grown sharply, and the financial and reputational damage from a single breach can be severe.
IT standards directly address this by providing structured guidance on where your vulnerabilities sit and how to fix them. They also make it far easier to demonstrate compliance when insurers, partners, or regulators ask for evidence of your security posture. As security-focused frameworks guide vulnerability identification, secure procedures, and regulatory compliance, they reduce the risk of a breach significantly.
The ACSC Essential Eight is the most relevant starting point for most Queensland SMEs. Here’s how its key controls map to real-world threats:
| Essential Eight control | What it protects against |
|---|---|
| Application control | Unauthorised or malicious software running |
| Patch applications | Known vulnerabilities being exploited |
| Configure Microsoft Office macros | Malware delivered via email attachments |
| User application hardening | Drive-by attacks from compromised websites |
| Restrict admin privileges | Attackers gaining elevated system access |
| Patch operating systems | OS vulnerabilities left unaddressed |
| Multi-factor authentication | Credential theft and account takeover |
| Regular backups | Ransomware and accidental data loss |
Statistic: The ACSC Essential Eight, when implemented at the highest maturity level, can prevent between 85% and 99% of the most common cyberattacks targeting Australian businesses.
That figure is significant. Most attacks on SMEs are not sophisticated. They rely on unpatched systems, weak passwords, and untrained staff. A structured framework like the Essential Eight closes those gaps methodically.
Here is a practical step-by-step process for using IT standards to identify and fix your cybersecurity risks:
- Map your assets: Know what devices, software, and data you hold. You cannot protect what you cannot see.
- Identify your highest-priority risks: Use the Essential Eight or ISO 27001 risk assessment process to rank your vulnerabilities by likelihood and impact.
- Set a baseline maturity level: The Essential Eight uses maturity levels one through three. Start at level one and build from there.
- Remediate your highest risks first: Patch critical software, enable multi-factor authentication (MFA) on all accounts, and restrict admin privileges.
- Document your controls: Written evidence of your security measures is essential for audits, insurance claims, and client assurance.
- Review quarterly: Threats evolve. Your controls need to keep pace. Schedule a formal review every three months.
When protecting sensitive data is a legal or contractual obligation, as it is for healthcare and financial services businesses, following a recognised standard also helps you demonstrate due diligence. It shows regulators and clients that your approach to security is systematic, not accidental. Smart service providers also use client-focused information security as a trust-building differentiator, and IT standards give you the substance to back that up.
Choosing and implementing IT standards for your business
Knowing the advantages, here’s how you can apply IT standards strategically for maximum impact. The biggest mistake most SMEs make is trying to implement everything at once.
Start by matching standards to your business size, sector, and current maturity. Here is a quick reference:
- Under 20 staff, low regulatory exposure: Start with SMB1001 and the ACSC Essential Eight at maturity level one.
- 20 to 100 staff, moderate regulatory exposure: Add ITIL service management practices to improve IT operations alongside Essential Eight at maturity level two.
- Healthcare, legal, or financial services: ISO 27001 becomes important, along with sector-specific compliance requirements such as the Privacy Act or Australian Privacy Principles.
- Growth-stage businesses: COBIT helps align IT governance with business strategy as your complexity increases.
Once you’ve chosen a standard, follow a structured implementation approach. Attempting to adopt multiple frameworks simultaneously without clear ownership creates confusion and often leads to abandonment. Formal IT implementation guidelines work best when approached in stages, with clear accountability and regular review points.
A stepwise implementation approach:
- Appoint an internal owner: One person needs to be accountable, even if external support is engaged. This ensures the initiative doesn’t stall.
- Conduct a gap analysis: Compare your current IT practices against the chosen standard. Identify where you meet requirements and where you fall short.
- Prioritise remediation by risk: Fix the highest-risk gaps first. Don’t waste time perfecting low-risk areas while critical vulnerabilities remain open.
- Document everything: Write down your processes, decisions, and controls. This is non-negotiable for most standards and invaluable for audits or staff transitions.
- Train your team: Technology controls only work if your staff understand why they exist. Training reduces workarounds and builds a genuine security culture.
- Schedule formal reviews: Set a date in the calendar every quarter to revisit your controls. Threats change. Business operations change. Your standards need to keep up.
Common mistakes to avoid:
- Overcomplicating early stages: A 10-person business does not need a 200-page security policy. Start lean and build out.
- Skipping staff training: Your staff are both your greatest asset and your greatest vulnerability. Untrained teams undermine even the best technical controls.
- Treating standards as a one-time project: Standards require ongoing maintenance. A set-and-forget approach creates a false sense of security.
- Ignoring vendor and supplier risk: Your standards need to extend to the third parties with access to your systems and data.
Pro Tip: Use the compliance guide for Queensland SMEs to map your current state against local regulatory requirements before committing to a specific framework. This saves you from choosing a standard that misses your most pressing obligations. You can also explore compliance and standards resources to compare frameworks side-by-side and identify the best fit for your industry.
What most Queensland SMEs get wrong about IT standards
Stepping back, here’s where many businesses miss the mark, and what experience shows really works.
Most SME owners treat IT as an expense to minimise rather than a capability to build. They call in support when something breaks, buy the cheapest solution that fixes the immediate problem, and move on. This approach feels cost-effective in the short term. In practice, it creates a system of accumulated shortcuts that becomes progressively more fragile and more expensive to maintain.
The uncomfortable truth is that piecemeal IT is not cheaper. It is just differently expensive. You pay in emergency support calls, extended downtime, staff frustration, data recovery costs, and eventually a breach that no one saw coming because there was no system to detect it. By contrast, businesses that invest in standardised IT routines early spend predictably rather than chaotically. They can also scale without rebuilding from the ground up every time they grow.
There is also a cultural element that gets overlooked. When IT operates on informal systems and unwritten rules, knowledge lives in people’s heads. If those people leave, the knowledge goes with them. Standards externalise that knowledge into documented processes that any competent person can follow. This makes your business more resilient and, frankly, more attractive to buyers, partners, and quality staff.
The other common misconception is that a breach will not happen to a business of your size. Cybercriminals specifically target SMEs because they tend to have weaker defences than large enterprises but often hold valuable client data. The benefits of structured IT support include not just better uptime but genuine resilience against the kinds of attacks that are increasingly targeting businesses exactly like yours.
Building standardised IT routines is not a bureaucratic exercise. It is one of the most concrete competitive advantages a Queensland SME can build, and the businesses getting ahead are the ones that recognise it before a breach forces the issue.
Need expert help with IT standards?
Selecting the right frameworks and actually embedding them into your business operations are two very different challenges. IT Start works with Queensland SMEs to bridge that gap, providing hands-on support for security implementation, compliance planning, and ongoing IT management. Whether you need to strengthen your defences through professional cyber security services, modernise your infrastructure with cloud solutions, or put reliable day-to-day business IT support in place, our team understands the specific pressures and obligations facing Brisbane businesses. We hold SMB1001 Gold certification, which means we practise what we recommend. Reach out for a no-obligation assessment and see exactly where your business stands.
Frequently asked questions
What are the most important IT standards for Queensland SMEs?
Key standards include ISO 27001, ITIL, ACSC Essential Eight, and the Australian SMB1001 standard, each addressing a different dimension of IT security and service management. Most Queensland SMEs benefit from starting with the ACSC Essential Eight and SMB1001 before expanding to more complex frameworks.
How do IT standards reduce business risk?
IT standards guide vulnerability identification, establish secure procedures, and support regulatory compliance, all of which directly reduce the likelihood and impact of a breach. They replace guesswork with tested, structured controls.
Can implementing IT standards help my business scale?
Yes, standardised processes reduce errors and redundancies, making it far simpler to add staff, systems, or locations without rebuilding your IT environment from scratch. Scalability becomes a planned outcome rather than a painful scramble.
Is it expensive to adopt IT standards for a small business?
The upfront investment varies depending on your starting point, but most SMEs find that efficiency gains and reduced downtime quickly offset implementation costs. The real cost is usually the breach or compliance failure that happens without standards in place.



