Australian businesses face a cyber incident every 6 minutes, yet the majority of small and medium enterprises across Queensland still operate without a documented response plan. That is a dangerous gap. When a breach hits, the difference between a minor disruption and a catastrophic loss often comes down to preparation. This guide walks you through exactly what a cyber incident response plan is, how to build one that meets Australian regulatory requirements, and how to tailor it to the real threats facing Queensland businesses right now. Whether you run a legal firm in Brisbane or a healthcare practice on the Gold Coast, this is essential reading.
Table of Contents
- What is a cyber incident response plan?
- Key components and lifecycle: NIST framework explained
- Australian and Queensland requirements: compliance and best practice
- Customising your response plan: playbooks, teams and testing
- Advanced challenges and expert tips for Queensland businesses
- Enhance your cyber resilience with IT Start
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Essential for all businesses | Every Queensland organisation needs a documented cyber incident response plan to comply with regulations and minimise impact. |
| Structured lifecycle matters | Follow recognised frameworks like NIST and ACSC Essential Eight for a comprehensive approach through preparation, response, and review. |
| Testing and updating is critical | Regular review, scenario testing, and team training keep your plan effective and compliant. |
| Prioritise rapid containment | Act quickly to isolate threats, reducing downtime and legal risk, and always retain forensics evidence. |
| Expert help optimises outcomes | Leveraging specialist support, such as IT Start, ensures your response plan meets both state and industry standards. |
What is a cyber incident response plan?
A cyber incident response plan, commonly called an IRP, is far more than a checklist. A documented strategy outlines how an organisation detects, responds to, analyses, contains, eradicates, recovers from, and learns from cybersecurity incidents. Think of it as your business’s emergency playbook for when things go wrong digitally.
The core goal is straightforward: minimise damage, keep your business running, and stay on the right side of the law. Many Queensland business owners assume an IRP is only relevant for large corporations with dedicated IT departments. That assumption is wrong and costly. Every organisation that holds customer data, processes payments, or relies on digital systems needs one.
A well-structured IRP covers the following phases:
- Detection: Identifying that an incident has occurred
- Response: Activating your team and initiating containment
- Analysis: Understanding the scope and nature of the threat
- Containment: Limiting the spread of damage
- Eradication: Removing the threat from your environment
- Recovery: Restoring systems and operations safely
- Post-incident review: Learning and improving from the event
“An incident response plan is not a luxury. It is the foundation of operational resilience for any business that depends on digital infrastructure.”
If you want to understand how cyber security response plans fit into your broader IT strategy, it helps to see the IRP as the reactive counterpart to your proactive security controls.

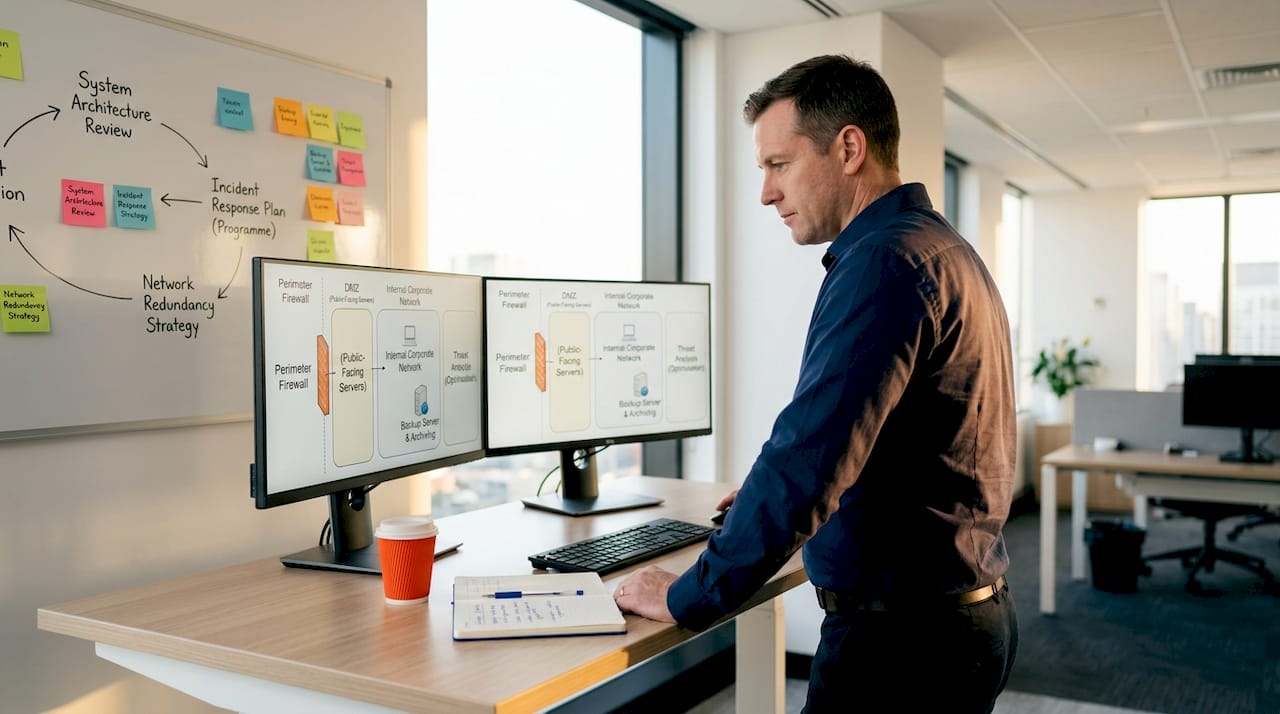
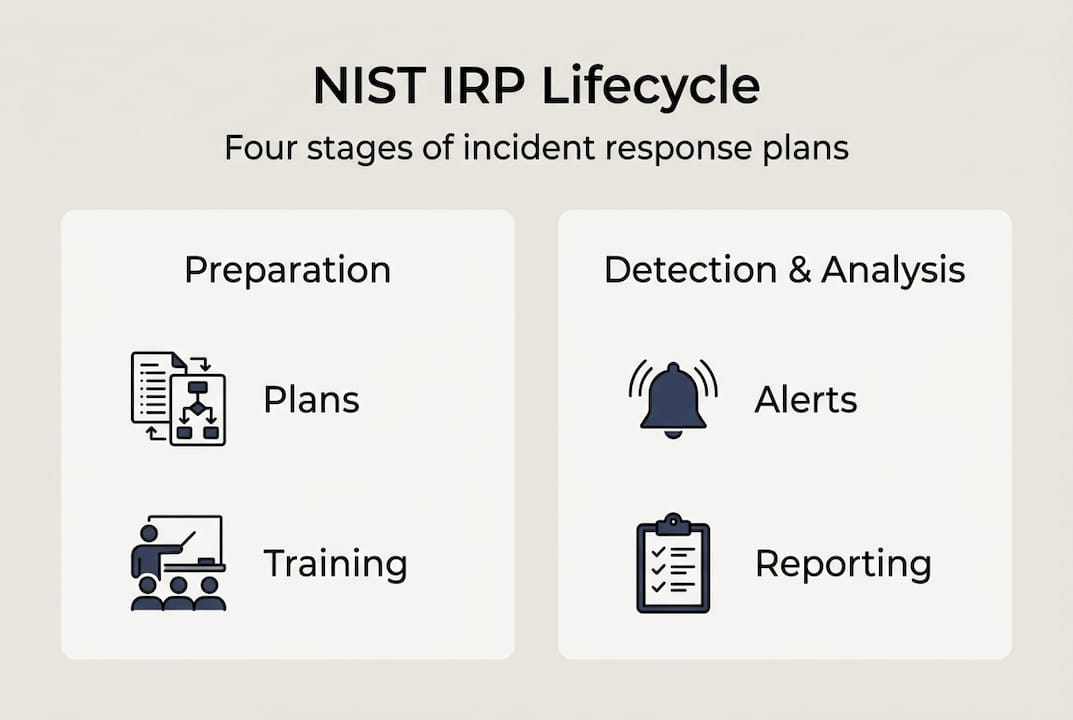
Key components and lifecycle: NIST framework explained
The most widely adopted standard for structuring an IRP is the NIST framework. NIST SP 800-61r3 defines four core lifecycle stages that give your response plan its backbone.
| NIST stage | What it involves | Key roles |
|---|---|---|
| Preparation | Policies, tools, training, communication plans | IT, Management, Legal |
| Detection and analysis | Monitoring, triage, incident classification | IT Security, SOC team |
| Containment, eradication, recovery | Isolate, remove, restore | IT, Operations, PR |
| Post-incident activity | Review, report, improve | All stakeholders |
Coordination across roles is critical. Your IT team cannot operate in isolation during a breach. Legal counsel needs to assess liability and notification obligations. Your communications or PR contact manages internal and external messaging. Without clear role assignments, response efforts collapse into confusion.
Here is a recommended sequence for building your response team structure:
- Appoint an Incident Response Manager to own the process end to end
- Assign technical leads for detection, containment, and recovery
- Include a legal representative familiar with Queensland privacy law
- Designate a communications lead for stakeholder and media contact
- Establish an escalation path for executive decision-making
Forensics and documentation are not optional extras. They are essential for compliance, insurance claims, and potential legal proceedings. The CREST incident management guide reinforces that preserving evidence during an incident is as important as stopping the attack itself.
Understanding the full range of cyber security methods available to your business will help you build a more robust detection and containment capability. Pairing your IRP with the ACSC Essential Eight guide gives you a strong technical foundation.
Australian and Queensland requirements: compliance and best practice
Queensland businesses operate under specific regulatory obligations that directly shape how your IRP must be structured. The Information Privacy Act 2009 (Qld) requires organisations to notify both the Office of the Information Commissioner (OIC) and affected individuals when a data breach is likely to cause serious harm. This is not optional.
The Queensland Government’s own breach response framework follows four clear steps: contain, assess, notify, and review. Aligning your IRP with this structure ensures you meet notifiable breach obligations under Queensland law without scrambling during a crisis.
The ACSC Essential Eight provides the technical controls that underpin a mature IRP. Businesses should aim to reach at least Maturity Level Two across all eight strategies. Here is how the two frameworks connect:
| Essential Eight control | IRP relevance |
|---|---|
| Application control | Reduces attack surface, limits incident scope |
| Patch applications | Prevents exploitation that triggers incidents |
| Multi-factor authentication | Slows attacker movement during a breach |
| Regular backups | Enables recovery phase of your IRP |
| Restrict admin privileges | Limits damage from insider threats |
Key benchmarks to track in your IRP include:
- MTTR (Mean Time To Respond): How quickly your team activates after detection
- MTTC (Mean Time To Contain): How fast you isolate the threat
- Annual plan review and post-incident review after every significant event
- Quarterly tabletop exercises to test team readiness
Pro Tip: Map your IRP directly to the NIST recommendations and the ACSC Essential Eight simultaneously. This dual alignment satisfies both international best practice and local compliance requirements in one structured effort.
For a deeper look at how to meet your obligations, explore IT compliance best practices and Essential Eight compliance resources tailored for Brisbane businesses.
Customising your response plan: playbooks, teams and testing
A generic IRP is better than nothing, but a scenario-specific playbook is what actually saves you during a real incident. Key methodologies include building playbooks for specific scenarios, running tabletop exercises quarterly, and integrating your IRP with your business continuity plan.
The four scenarios every Queensland business should have a playbook for:
- Ransomware: Step-by-step containment, backup restoration, and ransom decision protocol
- Phishing and credential theft: Account lockdown, password reset, and scope assessment
- Insider threat: Evidence preservation, HR involvement, and access revocation
- Supply chain compromise: Vendor isolation, third-party notification, and system audit
Your response team needs more than job titles. They need documented communication protocols, out-of-hours contact details, and pre-approved decision-making authority. During a live incident, nobody has time to ask who is allowed to shut down a server.
“Organisations that test their incident response plans quarterly recover significantly faster and with less financial damage than those that do not.”
Common pitfalls that undermine even well-written plans:
- Unclear role assignments that create bottlenecks under pressure
- Plans that have never been tested and fall apart in a real scenario
- No validation of backup recovery, meaning restoration fails when it matters most
- Failure to update the plan after staff changes or system upgrades
Pro Tip: Run a tabletop exercise with your leadership team before you finalise your IRP. Simulate a ransomware attack and walk through every decision point. You will quickly discover where your plan has gaps.
For practical guidance on keeping data safe and protecting Brisbane firm data, these resources offer sector-specific advice that complements your IRP.
Advanced challenges and expert tips for Queensland businesses
Most IRPs are built around external attackers. But the threat landscape is broader than that. Supply chain attacks account for 23% of incidents, and multi-surface attacks now affect 87% of organisations that experience a breach. Your plan must account for threats that originate inside your network or through trusted third parties.
Here are four expert-level actions to strengthen your IRP:
- Account for insider threats explicitly. Include HR and legal in your response team and define the evidence preservation process before an incident occurs.
- Prioritise rapid containment over eradication. Stopping the spread of damage is more urgent than fully removing the threat. Eradication can follow once containment is achieved.
- Retain forensic evidence. Do not wipe or rebuild systems before capturing logs, memory dumps, and network traffic data. This evidence is critical for legal proceedings and insurance claims.
- Prepare for AI-accelerated threats. Attackers are using AI to move faster and evade detection. Your monitoring tools and detection thresholds need to keep pace.
Pro Tip: Store a copy of your IRP offline and in a location that remains accessible even if your primary systems are compromised. A plan locked inside an encrypted server you cannot access is useless during a ransomware attack.
For Queensland businesses using cloud infrastructure, understanding cloud data security is a critical extension of your incident response capability. Cloud environments introduce unique containment and recovery challenges that your playbooks must address specifically.
The pace of threat evolution means your IRP is never truly finished. It is a living document that must grow with your business, your technology stack, and the threat landscape around you.
Enhance your cyber resilience with IT Start
Building an effective cyber incident response plan takes expertise, time, and a clear understanding of both local regulations and international best practice. That is exactly where IT Start comes in. We work with Queensland businesses across industries including financial services, healthcare, and legal to develop IRPs that are practical, compliant, and tested. Our team aligns your plan with the ACSC Essential Eight, Queensland privacy law, and NIST standards so you are covered from every angle. Explore our cyber security solutions and cloud services to see how we can support your business. Contact IT Start today for a consultation and take the first step toward genuine cyber resilience.
Frequently asked questions
Why do Queensland businesses need a cyber incident response plan?
Queensland regulations mandate notifiable breach reporting under the Information Privacy Act 2009, meaning even small businesses must have a documented plan to respond and report correctly when a breach occurs.
How often should a cyber incident response plan be reviewed?
Plans should be reviewed annually and immediately after any significant incident, with quarterly tabletop exercises to keep your team sharp and your procedures current.
What are the most common mistakes in cyber incident response planning?
Lack of testing, unclear roles, and failure to validate backup recovery are the three most damaging pitfalls, often turning a manageable incident into a prolonged crisis.
Are incident response plans only needed for large businesses?
Small businesses are frequently targeted and face the same privacy breach reporting obligations as large enterprises, making a documented IRP essential regardless of your organisation’s size.
Recommended
- What to do during a cyber attack: 2026 Brisbane guide – IT Start
- How to Enforce Cybersecurity for Brisbane Businesses – IT Start
- What you need for cyber security in Queensland SMEs 2026 – IT Start
- Practice Cyber Security for Brisbane SMEs: Step-by-Step Guide – IT Start
- Understand cyber threats in business security 2026