Many small to medium businesses mistakenly believe network access control is an outdated security approach, replaced by newer technologies. This misconception puts Queensland SMBs at serious risk. Network access control remains vital for protecting networks, especially as BYOD policies, remote work, and IoT devices expand attack surfaces. This guide explains what NAC is, why it matters for your business, and how you can apply it to enhance both security and operational efficiency without falling into common deployment traps.
Table of Contents
- Understanding Network Access Control Basics
- Why Network Access Control Matters For Queensland SMBs
- Modern NAC Features And Deployment Best Practices
- Avoiding Mistakes: Common Challenges In NAC Implementation
- How IT Start Can Support Your Network Access Control Needs
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| NAC validates access | Network access control verifies devices and users meet security policies before granting network entry. |
| Risk reduction | Implementing NAC prevents non-compliant or unauthorised devices from accessing your network, reducing breach likelihood. |
| Modern flexibility | NAC supports BYOD, remote work, and IoT environments through dynamic policy enforcement and automated compliance checks. |
| Deployment discipline | Successful NAC requires clear objectives and phased rollout to avoid business disruption and user lockouts. |
| Operational gains | Automation through NAC improves efficiency by streamlining device onboarding and enforcing policies consistently. |
Understanding network access control basics
Network access control regulates access by enforcing policies and ensuring only compliant devices and authorised users connect. Think of NAC as a security checkpoint that examines every device and user trying to enter your network, verifying their identity and checking whether they meet your security standards before granting access.
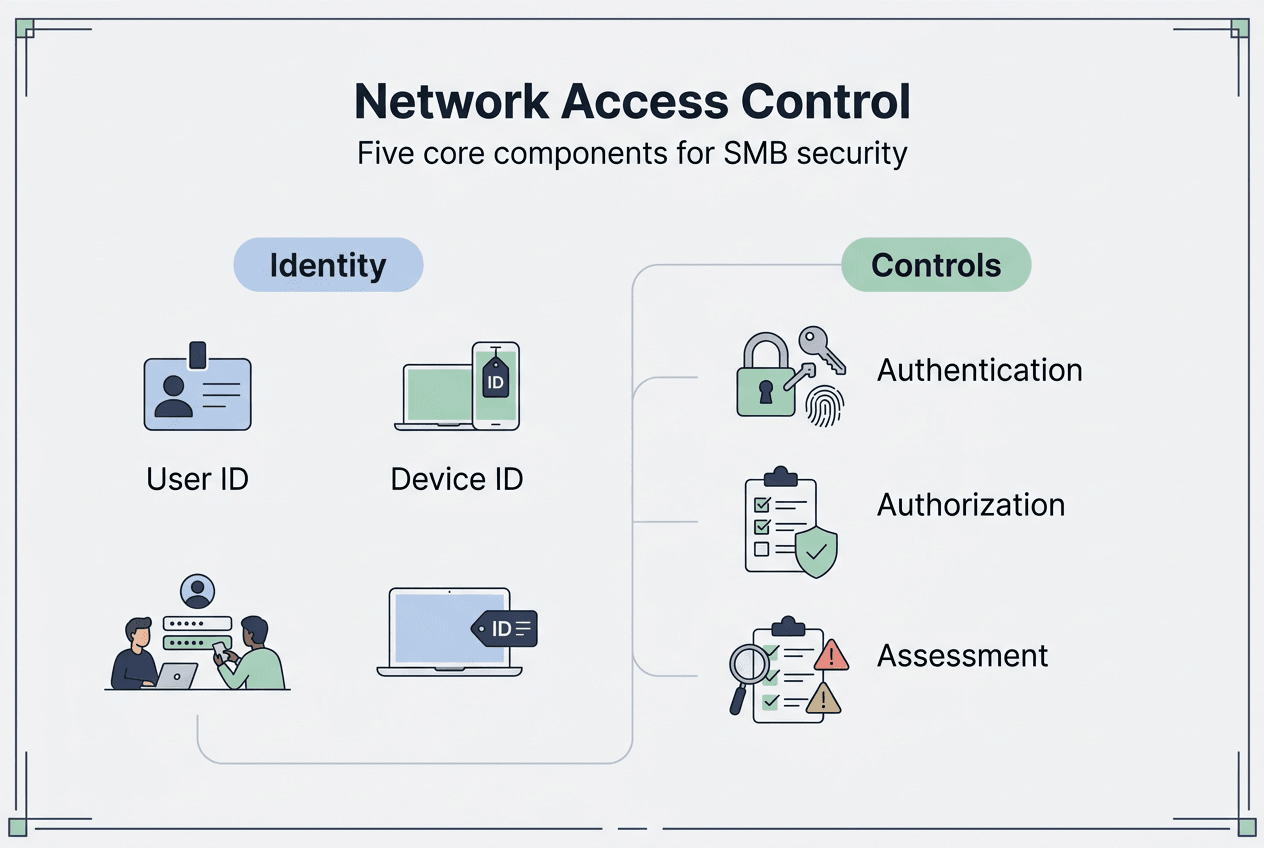
NAC operates through five core components working together. These components include identification, authentication, authorisation, posture assessment, and remediation. Identification determines who or what is requesting access. Authentication verifies the claimed identity through credentials or certificates. Authorisation decides what level of access the authenticated entity receives based on policies you define.
Posture assessment examines the device’s security health, checking for updated antivirus software, current patches, and proper configurations. Remediation handles non-compliant devices by either blocking access entirely or directing them to a quarantine network where they can address security gaps before joining your main network. Understanding access control fundamentals helps you recognise how NAC fits within your broader security strategy.
NAC integrates with network elements like switches, wireless access points, VPN gateways, and policy servers. This integration allows NAC to enforce decisions across your entire infrastructure consistently. For Queensland SMBs managing multiple locations or supporting remote workers, this centralised control becomes especially valuable.
The system enforces policies automatically, removing the burden of manual verification from your IT team. As employees bring personal devices to work or connect IoT equipment like security cameras and smart thermostats, NAC ensures each connection meets your security requirements. This foundational approach to network security becomes critical as your technology environment grows more complex.
Key NAC capabilities include:
- Automated device discovery and inventory management
- Real-time compliance verification before network access
- Dynamic network segmentation based on user roles and device types
- Guest access provisioning with self-service portals
- Integration with existing authentication systems and security tools
Why network access control matters for Queensland SMBs
Queensland SMBs face mounting cybersecurity challenges as work patterns evolve. Remote work arrangements, BYOD policies, and expanding IoT deployments create numerous entry points for potential attacks. Each unmanaged device connecting to your network represents a possible vulnerability that attackers can exploit to gain initial access.
NAC addresses these risks by blocking unauthorised or non-compliant devices before they can interact with sensitive systems. When an employee’s personal laptop lacks current security patches or a contractor’s tablet runs outdated antivirus software, NAC prevents these devices from accessing your network until the issues are resolved. This proactive stance dramatically reduces your attack surface.

Research shows NAC can reduce security incidents by up to 60% within the first year for SMBs. This reduction stems from NAC’s ability to enforce consistent security policies across all connection types, whether employees work from the office, home, or client sites. The financial impact of prevented breaches far outweighs NAC implementation costs for most businesses.
Consider that 70% of Australian SMBs allow BYOD, highlighting NAC’s importance for secure device onboarding. Without proper controls, each personal device becomes a potential gateway for malware, ransomware, or data exfiltration. NAC creates a structured process for bringing these devices onto your network safely.
Beyond preventing initial breaches, NAC stops lateral movement within your network. If an attacker compromises one device, NAC’s segmentation capabilities prevent them from freely exploring your entire infrastructure. Different network segments can enforce different security policies, limiting what compromised devices can access. Implementing strong network security practices becomes manageable through NAC automation.
NAC also supports compliance requirements many Queensland businesses face. Industries like healthcare, finance, and legal services must demonstrate they control who accesses sensitive data and how. NAC provides audit trails showing exactly which devices connected, when they connected, and what policies they satisfied. This documentation proves invaluable during compliance audits or incident investigations.
The secure self-service portals NAC provides improve user experience while maintaining security. Employees and guests can onboard their devices independently without waiting for IT assistance, following guided workflows that ensure compliance. This balance between security and convenience drives adoption and reduces support tickets.
Critical NAC benefits for SMBs include:
- Automated enforcement of security policies across all devices
- Reduced risk from BYOD and contractor devices
- Compliance support through detailed access logs and policy enforcement
- Improved operational efficiency via self-service onboarding
- Prevention of lateral movement following initial compromise
Modern NAC features and deployment best practices
NAC has evolved to support hybrid, BYOD, and IoT environments and remains a key enforcement mechanism for Zero Trust architecture. Modern NAC solutions go far beyond simple port-based access control, offering sophisticated capabilities that address current security challenges.
Today’s NAC systems support dynamic network segmentation, automatically placing devices into appropriate network zones based on their type, user identity, and compliance status. A managed company laptop might access all internal resources, while a personal tablet connects only to specific applications through a restricted segment. This granular control happens automatically based on policies you define once.
Certificate-based passwordless authentication represents another significant advancement. Instead of relying on easily compromised passwords, modern NAC can use digital certificates to verify device and user identity. This approach eliminates password-related vulnerabilities while streamlining the authentication process for users.
NAC integrates seamlessly with authentication protocols like 802.1X and RADIUS, working with your existing infrastructure rather than requiring complete replacement. This integration extends to security information and event management systems, threat intelligence platforms, and mobile device management solutions, creating a coordinated security ecosystem.
| Feature | Traditional NAC | Modern NAC |
|---|---|---|
| Primary focus | Port-based access control | Identity and context-based access |
| Device support | Managed corporate devices | BYOD, IoT, guests, contractors |
| Enforcement | Static policies | Dynamic, risk-based policies |
| Authentication | Passwords and basic credentials | Certificates, multi-factor, passwordless |
| Architecture | On-premises appliances | Cloud-managed, hybrid deployment |
| Integration | Limited third-party connections | Extensive API ecosystem |
Deploying NAC successfully requires following proven best practices. Premature enforcement during deployment often causes failures such as users being locked out or business disruptions. Start by defining clear objectives for what you want NAC to achieve, whether that’s BYOD security, compliance support, or IoT management.
Begin deployment in monitor-only mode, observing network traffic and device behaviour without blocking anything. This visibility phase helps you understand your current environment, identify all devices connecting to your network, and spot potential policy conflicts before enforcement begins. Most successful deployments spend several weeks in this phase.
Gradually introduce enforcement, starting with less critical network segments or device types. Guest wireless networks make excellent initial enforcement targets because they carry lower business risk if problems arise. Once you’ve refined policies and processes, expand enforcement to employee devices and finally to critical infrastructure.
Pro tip: Prioritise NAC solutions that integrate with your current security infrastructure for smoother management and better overall protection through coordinated responses.
Essential deployment steps include:
- Document current network topology and device inventory
- Define specific security policies for different device types and user roles
- Configure NAC in visibility mode initially
- Test policies thoroughly in isolated environments
- Phase enforcement gradually across network segments
- Train users on new onboarding processes
- Establish ongoing monitoring and policy refinement processes
Improving your network security becomes achievable when you approach NAC as a program requiring continuous attention rather than a one-time project.
Avoiding mistakes: common challenges in NAC implementation
NAC deployment failure often results from vague objectives, poor planning, or enabling full enforcement too early. Understanding these pitfalls helps Queensland SMBs avoid costly mistakes and achieve NAC success.
Undefined goals represent the most common failure point. Organisations deploy NAC without clearly articulating what problems they’re solving or what success looks like. This ambiguity leads to scope creep, conflicting requirements, and ultimately abandoned projects. Before purchasing any NAC solution, document specific outcomes you expect to achieve.
Weak integration with existing systems creates operational headaches and security gaps. If your NAC doesn’t communicate properly with your authentication directory, device management platform, or security monitoring tools, you’ll struggle to maintain consistent policies. Evaluate integration capabilities thoroughly during solution selection.
Misconfigurations can immediately impact business operations, blocking legitimate users or allowing unauthorised access. A single incorrect policy rule might prevent executives from accessing email or lock out remote workers entirely. These disruptions erode trust in the NAC system and often lead to policies being relaxed or disabled.
Premature enforcement compounds misconfiguration risks. Switching from monitor mode to full enforcement before thoroughly testing policies guarantees problems. Users get locked out, critical devices lose connectivity, and IT teams face overwhelming support demands. The resulting chaos often kills NAC projects that could have succeeded with patience.
Insufficient ongoing management causes NAC effectiveness to decay over time. As your business adds new applications, devices, and users, policies must evolve to accommodate changes while maintaining security. NAC requires continuous attention, not just initial setup. Proper network security administration includes regular NAC policy reviews and updates.
To mitigate these risks, follow this structured approach:
- Define clear, measurable outcomes for your NAC deployment, such as reducing unauthorised device connections by 95% or achieving specific compliance requirements.
- Start with comprehensive visibility mode, spending adequate time understanding your network environment and identifying all devices and connection patterns.
- Integrate NAC carefully with existing authentication, security, and management systems, testing all connections thoroughly before relying on them.
- Phase enforcement gradually, beginning with low-risk segments and expanding only after validating policies work correctly without disrupting legitimate access.
- Establish ongoing management processes including regular policy reviews, quarterly access audits, and continuous monitoring of NAC logs for anomalies.
- Document all policies, exceptions, and procedures so knowledge isn’t concentrated in one person who might leave your organisation.
Pro tip: Treat NAC as an ongoing program rather than a one-time project to ensure continuous alignment with business needs and evolving security threats.
Common warning signs your NAC implementation needs attention include increasing support tickets related to network access, growing lists of policy exceptions that undermine security, devices connecting that shouldn’t be allowed, or compliance gaps appearing in audit reports. Address these signals promptly before they escalate into serious problems.
How IT Start can support your network access control needs
Navigating NAC deployment and management requires expertise many Queensland SMBs lack internally. IT Start provides comprehensive cyber security services designed specifically for Brisbane-based businesses facing these challenges. Our team understands the unique security landscape Queensland SMBs operate within, from industry compliance requirements to the practical realities of limited IT resources.
We offer tailored business IT support that includes NAC assessment, deployment planning, and ongoing management. Rather than generic solutions, we evaluate your specific environment, business requirements, and risk profile to recommend appropriate NAC approaches. Our proactive support model ensures your NAC policies evolve alongside your business.
Our cloud services integrate seamlessly with NAC implementations, supporting hybrid environments where some resources live in the cloud while others remain on premises. This integration ensures consistent security policies regardless of where your data and applications reside.
Contact IT Start to assess your network access control needs and develop a deployment strategy that avoids common pitfalls while maximising security effectiveness. Our local Brisbane presence means we understand Queensland business challenges firsthand and can provide responsive support when you need it.
Frequently asked questions
What is the difference between network access control and firewall?
NAC controls who and what devices can connect to your network based on identity verification and compliance with security policies. Firewalls monitor and filter traffic passing through the network, blocking malicious data packets and unauthorised connection attempts. Both serve complementary but distinct security functions, with NAC handling the initial access decision and firewalls managing ongoing traffic.
Can small businesses in Queensland afford to implement NAC?
NAC solutions are scalable and can be tailored to SMBs in Queensland with varying budgets and technical requirements. Many vendors offer cloud-managed NAC that reduces infrastructure costs and simplifies deployment for smaller organisations. The investment typically pays for itself through reduced security incidents, with IT compliance benefits adding further value.
How does NAC support compliance with industry regulations?
NAC verifies device and user compliance before granting network access, enforcing security policies required by various laws and standards. It provides detailed audit trails showing who accessed what resources and when, supporting compliance reporting for frameworks like APRA CPS 234 or healthcare privacy requirements. Continuous monitoring capabilities help you demonstrate ongoing compliance rather than point-in-time assessments.
What are best practices for maintaining NAC once deployed?
Continuously update policies as your business needs and threat landscape evolve, reviewing them at least quarterly. Regularly monitor NAC logs to identify anomalies, policy violations, or emerging patterns that require attention. Never consider NAC deployment a finished project; ongoing management ensures policies remain effective and aligned with business objectives while adapting to new devices, applications, and security challenges.

