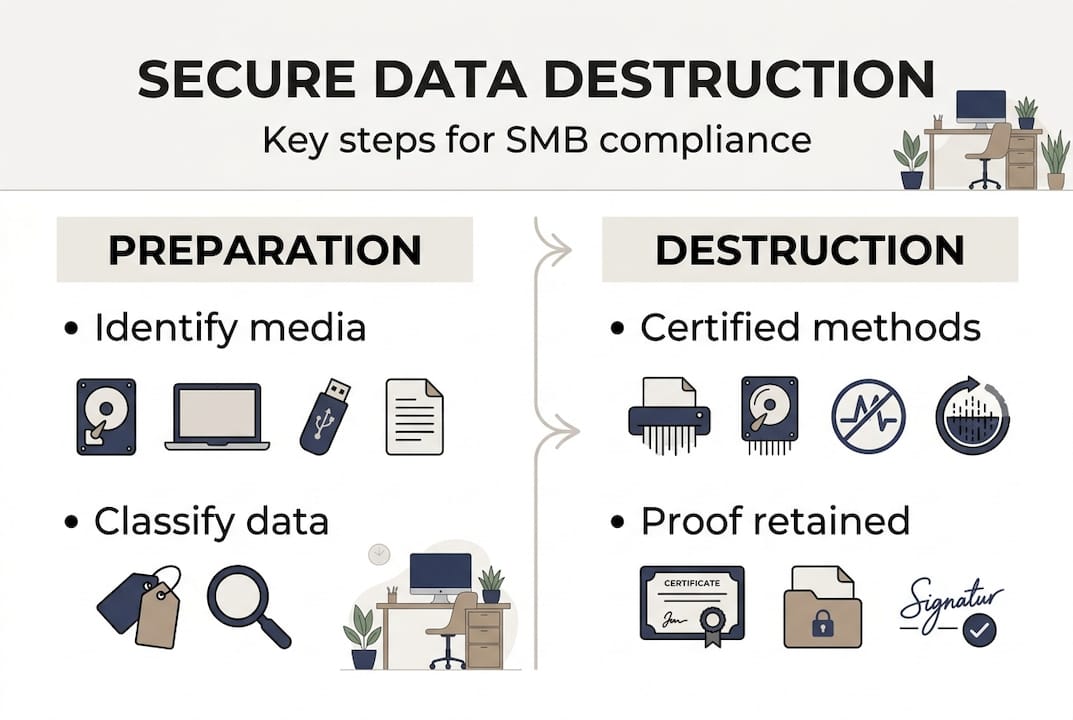
TL;DR:
- Secure data destruction is essential to comply with Australian privacy laws and protect personal information.
- Certified methods like physical shredding and digital erasure, with proper documentation, are required for compliance.
- Most SMBs overlook end-of-life data handling, risking fines, breaches, and loss of client trust.
Pressing delete does not destroy data. Neither does emptying the recycle bin, reformatting a drive, or tossing an old laptop into a skip bin. For Queensland small and medium-sized businesses, this misunderstanding carries serious consequences, including privacy breaches, regulatory fines, and permanent damage to client trust. Australia’s Privacy Act and the Australian Privacy Principles place clear obligations on businesses to properly destroy personal information when it is no longer needed. This guide explains what secure data destruction actually means, which methods meet compliance requirements, how to choose a certified provider in Queensland, and what steps to take right now to close the gaps in your data lifecycle.
Table of Contents
- Why secure data destruction matters for Queensland SMBs
- Understanding destruction methods: What really works?
- Choosing a certified provider in Queensland
- Putting secure destruction into practice: Steps for SMBs
- What most companies miss about secure data destruction
- Get expert help with secure destruction for your business
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Legal necessity | Australian privacy law requires SMBs to securely destroy personal information when no longer needed. |
| Certified methods | Secure destruction means using NIST-compliant or NAID AAA certified providers to avoid compliance pitfalls. |
| Proof is power | Always demand a certificate of destruction to demonstrate compliance and protect your business in audits. |
| Tailored action | Implementation should involve regular review, staff training, and clear documentation of destruction events. |
Why secure data destruction matters for Queensland SMBs
Personal information is defined broadly under Australian law. It includes names, addresses, phone numbers, email addresses, financial details, health records, and any data that could identify an individual. If your business collects, stores, or processes this kind of information, and almost every Queensland SMB does, then you are legally required to protect it and destroy it properly when it is no longer needed.
Australian Privacy Principle 11 is the key regulation here. APP 11 guidelines require organisations to take reasonable steps to protect personal information from misuse, interference, and loss, and to destroy or de-identify it when it is no longer required for any purpose. “Reasonable steps” is not a vague suggestion. It means using methods that actually work.
The consequences of getting this wrong are real. The Office of the Australian Information Commissioner (OAIC) has the power to investigate complaints, issue determinations, and seek civil penalties. For serious or repeated breaches, penalties can reach into the millions. Beyond fines, a data breach involving improperly disposed information can trigger mandatory notification obligations, media scrutiny, and lasting client trust loss.
Here is what Queensland SMBs most often overlook:
- Customer records stored on retired computers or servers that were simply wiped and resold
- Paper documents shredded with a basic strip-cut office shredder that can be reconstructed
- Old backup drives sitting in storage rather than being securely destroyed
- Cloud accounts that are closed without properly sanitising the data first
A useful fact to keep in mind: studies show that a significant proportion of second-hand hard drives still contain recoverable personal data when resold or discarded without certified destruction. This is not a theoretical risk. It is a documented pattern that regulators take seriously.
For a broader view of your obligations, data protection best practices for Queensland SMBs cover the wider landscape of privacy compliance beyond just destruction.
Pro Tip: Always request a certificate of destruction from any provider you engage. This document is your written evidence that data was destroyed in a compliant manner, and it is essential if you ever face an audit or a complaint.
Understanding destruction methods: What really works?
The biggest misconception in this space is that deleting a file removes it. It does not. When you delete a file, the operating system simply marks that space as available. The data remains physically on the drive until it is overwritten, and even then, certain recovery tools can reconstruct fragments. Reformatting has the same limitation. For certified compliance, you need methods that go much further.
NIST secure methods under NIST SP 800-88 define three categories of media sanitisation:
- Clear: Software-based overwriting that protects against standard recovery tools. Suitable for lower-risk data on functioning drives.
- Purge: Degaussing (using powerful magnetic fields) or cryptographic erasure. More thorough than Clear, and suitable for higher-risk data.
- Destroy: Physical destruction such as shredding, disintegration, or incineration. The most secure option and the recommended approach for end-of-life media.
Here is a simple comparison to help you choose:
| Method | Security level | Works on HDD | Works on SSD | Best use case |
|---|---|---|---|---|
| Clear (overwrite) | Moderate | Yes | Partially | Reuse within organisation |
| Purge (degauss) | High | Yes | No | End-of-life HDDs |
| Purge (crypto erase) | High | No | Yes | End-of-life SSDs |
| Destroy (shred/disintegrate) | Highest | Yes | Yes | All end-of-life media |
One important nuance: degaussing does not work on solid state drives (SSDs). SSDs store data differently to traditional hard disk drives, and a magnetic field has no effect on flash memory chips. This is a common and costly mistake. For SSDs, the correct approach is either certified cryptographic erasure using a system like Blancco, or physical destruction.
Blancco is widely regarded as an industry standard for software-based effective data security. It produces a tamper-proof, auditable erasure certificate for each device processed, which means it satisfies compliance requirements under the Privacy Act and can support APRA-regulated organisations in meeting their data governance obligations. Simply running a wipe utility you downloaded from the internet does not produce this level of documented proof.

For computer security basics around media handling, the key principle is this: match the destruction method to the media type, the sensitivity of the data, and the compliance requirements of your industry.
Pro Tip: SSDs require a different approach to HDDs. Before engaging any provider, confirm they use a certified method specifically validated for your media type, not a one-size-fits-all process.
Choosing a certified provider in Queensland
Knowing the right methods is only part of the picture. Who carries out the destruction matters just as much. Engaging an uncertified contractor, even a well-intentioned one, leaves you exposed. If a breach occurs and you cannot demonstrate that a compliant process was followed, the liability stays with your business.
The benchmark certification to look for is NAID AAA. NAID (the National Association for Information Destruction) conducts unannounced audits of its certified members to verify that their destruction processes, security controls, and staff screening meet strict standards. A NAID AAA certification is internationally recognised and aligns with APP 11 compliance.
Here is a simple checklist when vetting a provider:
- Confirm NAID AAA certification and ask to see current documentation
- Ask whether destruction is on-site (at your premises) or off-site (at their facility)
- Verify which media types they handle, including paper, HDDs, SSDs, USB drives, and mobile devices
- Confirm that a certificate of destruction is issued for every job
- Check whether they provide chain-of-custody documentation from collection to destruction
Endeavour Foundation provides NAID AAA certified shredding across Queensland, making them a strong option for SMBs seeking compliant paper and media destruction with a social enterprise benefit. Shred-X is another well-known provider operating throughout Queensland with on-site and off-site options for both paper and digital media.
| Provider | Certification | Media types | On-site option | QLD coverage |
|---|---|---|---|---|
| Endeavour Foundation | NAID AAA | Paper, some digital | Yes | Wide |
| Shred-X | NAID AAA | Paper, digital, IT assets | Yes | Wide |
| Local IT asset disposal firms | Varies | Digital, IT assets | Sometimes | Regional |
“Always obtain certificates for every destruction event. A certificate is not just paperwork. It is your legal evidence that the obligation was met.”
For businesses in regulated industries such as healthcare, legal, and financial services, certificates of destruction are not optional extras. They form part of your compliance record and should be retained in line with your document management policy. APP 11 compliance depends on being able to demonstrate, not just claim, that data was handled correctly.
Putting secure destruction into practice: Steps for SMBs
Knowing the theory is useful. Having a repeatable process embedded in your business is what actually protects you. Here is how to build one:
- Identify what needs to be destroyed. Conduct a data audit to map where personal information lives across your business, including physical files, local drives, servers, portable media, cloud storage, and employee devices.
- Classify your data. Not all information carries the same risk. Health records and financial data require a higher level of destruction than general correspondence. Assign destruction methods accordingly.
- Select the right method and provider. Use the NIST SP 800-88 framework to match method to media type. Engage a NAID AAA certified provider for physical destruction and a certified software tool like Blancco for digital sanitisation requiring documented proof.
- Document everything. Collect certificates of destruction for each event. Log the date, media type, quantity, method used, and provider details. This is your audit trail.
- Include cloud data. Closing a cloud account is not the same as destroying the data. Work with your provider to confirm data deletion and obtain written confirmation where possible.
- Train your team. Staff need to understand what counts as sensitive information, why it matters, and what to do when equipment is retired or documents are no longer needed.
Data loss prevention tactics for Brisbane SMBs reinforce that human error remains one of the leading causes of data incidents, and training is a practical safeguard. Likewise, regularly reviewing protecting your business data helps you catch gaps before they become breaches.
For APP 11 compliance, using NAID AAA certified providers and maintaining certificates for every destruction event is the clearest way to demonstrate that reasonable steps were taken.
Pro Tip: Set a regular destruction schedule, quarterly or at the end of each financial year, and tie it to your wider privacy policy review. Treating destruction as a routine business process rather than a one-off task is far more reliable.
What most companies miss about secure data destruction
Most Queensland SMBs focus their security efforts on active systems: firewalls, antivirus, cloud backups, access controls. That is sensible. But data security does not end when a device is retired or a contract is finished. The end of a data lifecycle is where some of the biggest, and most avoidable, risks sit.
One thing we see repeatedly is businesses relying on their general IT provider or a cleaning contractor to “wipe” old equipment, with no certification, no auditable process, and no certificate of destruction. The intention is good. The outcome is not compliant. A wipe performed without a certified tool like Blancco produces no evidence, and data can often still be recovered.
Certificates of destruction are not red tape. In the event of a regulatory investigation or a privacy complaint, they are the difference between demonstrating compliance and being unable to prove anything at all. Without that documented trail, good intentions count for very little.
Leadership ownership matters here too. When the responsibility for data destruction sits with a junior staff member or is assumed to be “someone else’s job,” it falls through the cracks. Building it into policy, assigning clear accountability, and reviewing it regularly is what separates businesses that manage risk from those that discover it too late. For practical business data security tips, leadership accountability is consistently one of the highest-impact factors.
Get expert help with secure destruction for your business
At IT Start, we work with Queensland SMBs to close the gaps in their data security lifecycle, from active systems through to compliant end-of-life destruction. If you are unsure whether your current destruction practices meet APP 11 requirements or industry standards like APRA, we can help you assess your situation and build a process that holds up under scrutiny. Our cyber security solutions cover the full picture, and our cloud data management services ensure that digital data is handled correctly at every stage. Reach out to IT Start for a no-obligation conversation about your compliance posture and what certified secure destruction looks like for your business.
Frequently asked questions
What is the most secure data destruction method for hard drives?
Physical destruction such as shredding is the most secure option, particularly when NIST SP 800-88 guidelines are followed for end-of-life media. Certified shredding leaves no recoverable data.
Are certificates of destruction really needed for SMBs in Queensland?
Yes. Certificates provide documented proof of APP 11 compliance and are essential evidence during audits or regulatory investigations.
Does deleting files or formatting drives comply with Australian privacy law?
No. Deleting or reformatting does not sufficiently destroy data. Certified physical or verified digital methods are required to meet Privacy Act obligations.
Can regular office shredders be used for document destruction?
Standard office shredders rarely meet compliance standards. NAID AAA certified services such as Endeavour Foundation are recommended for sensitive business documents.
Is secure destruction needed for cloud data?
Yes. APP 11 also applies to cloud-stored personal information, and businesses must confirm data is properly sanitised when cloud services are decommissioned.
Recommended
- SMB data protection best practices for Queensland businesses – IT Start
- How to Protect Sensitive Data for Brisbane SMEs – IT Start
- How to Keep Data Secure: Essential Steps for 2025 – IT Start
- 7 Essential Steps for a Data Protection Checklist for SMEs – IT Start
- How to Secure Your Data: Essential Steps for Protection – buy2fix
- Insurance Data Security Best Practices for Modern Insurers



