TL;DR:
- IT compliance failures in Queensland businesses can lead to hefty fines, client trust issues, and operational halts due to cyber threats. Small and medium enterprises often struggle with frameworks like the Essential Eight and SMB1001, but adopting continuous, documented controls enhances security and credibility. Proactive compliance, ongoing review, and expert support are vital for reducing risks and winning client contracts.
IT compliance failures cost Queensland businesses more than money. A single breach can trigger significant regulatory fines, destroy hard-won client relationships, and in the worst cases, bring operations to a standstill while ransomware attackers hold your data hostage. Yet many small and medium enterprises across Queensland are still unclear on where to start, which frameworks apply to them, and how to keep up with evolving requirements. This guide cuts through the confusion and gives you a clear, actionable path to better IT compliance, drawing on frameworks and best practices built specifically for businesses like yours.
Table of Contents
- Understanding the compliance challenge for Queensland SMEs
- Preparing your IT compliance strategy: Steps and essentials
- Core actions: Implementing Essential Eight and SMB1001 controls
- Verifying and improving compliance: Assurance, evidence and ongoing review
- Why a proactive compliance mindset beats the audit rush
- Enhance your compliance journey with local IT specialists
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Adopt proven frameworks | Follow the Essential Eight and SMB1001 standards to lift your SME’s IT compliance posture. |
| Make compliance continuous | Treat compliance as an ongoing programme with regular checks and fresh documentation, not a once-a-year event. |
| Customise controls when needed | Alternate controls are allowed for edge cases but must be formally justified and approved. |
| Keep strong evidence | Document every control and audit to prove due diligence and support future assurance. |
| Seek local expert support | Engaging a Queensland IT partner ensures your compliance efforts stay effective and up-to-date. |
Understanding the compliance challenge for Queensland SMEs
IT compliance means having documented, verified, and consistently enforced controls that protect your systems, data, and clients from cyber threats and regulatory breaches. For Queensland SMEs, this is no longer optional background noise. Supply chain requirements, government contract obligations, and tightening privacy regulations mean that your compliance posture is increasingly visible to clients, insurers, and auditors.
The risks are real and growing. A data breach can trigger penalties under the Privacy Act, damage trust with clients who may move to competitors, and expose you to liability if customer data is compromised. Beyond fines, the operational cost of recovering from a cyber incident often far outweighs the investment in prevention. Many Queensland SMEs also face requirements from larger clients or government agencies requiring evidence of baseline security controls before contracts are signed.
Two frameworks dominate the local conversation. The Australian Cyber Security Centre recommends you use the Essential Eight as the technical benchmark and focus on continuous enforcement for protecting business systems. The SMB1001 certification standard is a structured, tiered cybersecurity certification designed specifically for small and medium practices, and Queensland Law Society recommends pursuing Gold for robust cyber assurance.
Understanding how these compliance management systems fit together is a smart first move before building your programme. A practical IT compliance guide can help you map which framework best suits your industry and risk profile.
Key triggers that commonly prompt Queensland SMEs to start their compliance journey:
- A client or government agency requesting proof of cyber security controls before contract award
- A near-miss security incident or successful phishing attack
- Cyber insurance renewal requiring evidence of baseline practices
- New staff handling sensitive customer data
- Moving to cloud-based systems or third-party software platforms
| Feature | Essential Eight | SMB1001 |
|---|---|---|
| Designed for | All Australian businesses and government | Small and medium enterprises specifically |
| Structure | Eight technical mitigation strategies | Tiered certification (Bronze, Silver, Gold) |
| Focus | Technical controls and patching cadences | Holistic cyber hygiene and business practices |
| Certification available? | No formal certification | Yes, formal third-party certification |
| Best suited to | Technical baseline enforcement | Demonstrating due diligence to clients |
| Recommended by | ACSC, Queensland Government | QLS, professional services regulators |
Understanding IT’s role in compliance is the foundation for everything else. Once you know what each framework covers and why, building your programme becomes much more manageable.
“The question isn’t whether Queensland SMEs can afford to invest in compliance. It’s whether they can afford not to, given the financial and reputational cost of getting it wrong.”
Preparing your IT compliance strategy: Steps and essentials
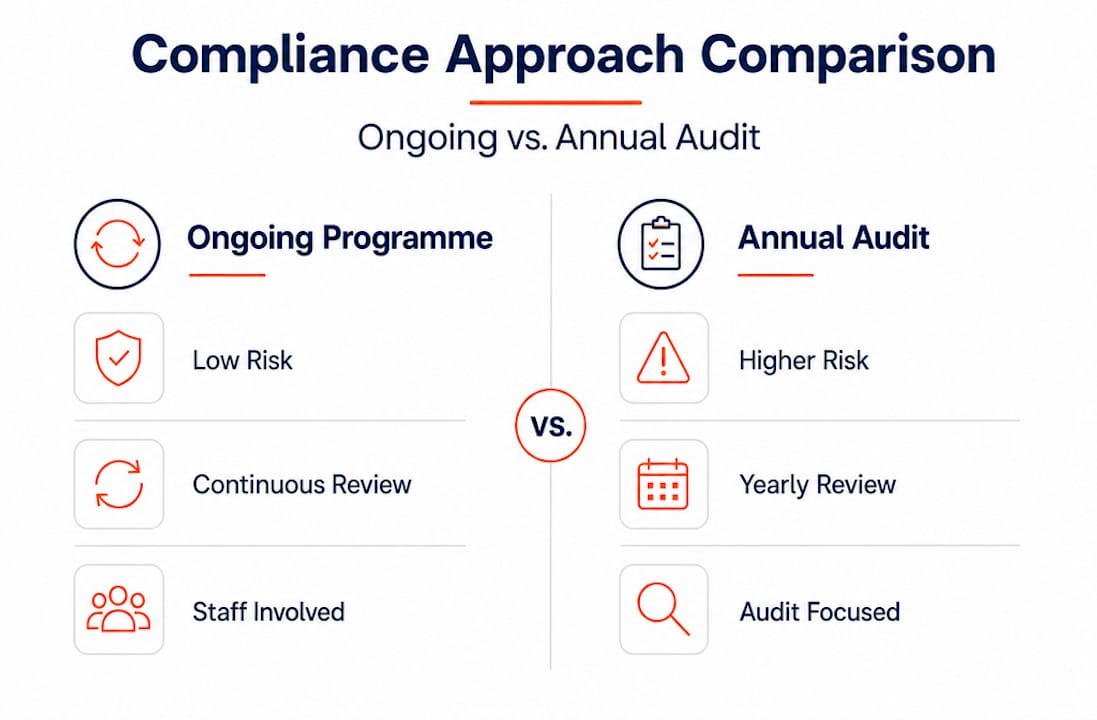
With the major frameworks clear, the next step is laying strong compliance foundations. A common mistake is treating compliance as a single event, like an annual audit. The cyber security guidelines from the ACSC are clear: treat compliance as a continuous control programme with ongoing risk-based monitoring, assurance, and documentation including strategy documents, plans, assessment reports, and action milestones rather than just periodic audits.
Start by defining your compliance requirements. Ask what data you hold and who it belongs to, which clients or contracts require evidence of specific controls, and what industry regulations apply to your sector. A healthcare practice handles different risks than a legal firm or an accounting business, but all of them operate in Queensland under the same Essential Eight framework as baseline.
Must-have compliance documentation for any Queensland SME:
- A written cyber security policy and risk register
- An asset register covering all hardware, software, and data stores
- Documented procedures for access control and password management
- Patch management logs with dates and applied versions
- Backup and recovery test results
- Incident response plan and contact list
- Evidence of staff training completion
- Assessment reports and remediation action logs
Assigning clear ownership matters. Compliance cannot live only in the IT team’s inbox. Every staff member who handles data, accesses systems, or communicates with clients has a role to play. Assign a compliance owner, document responsibilities in writing, and make sure your team understands why these controls exist, not just how to follow them.

Checking compliance standards for Queensland SMEs helps you understand which specific requirements apply to your business type and size.
Pro Tip: Set a monthly calendar reminder to review one area of your compliance documentation. Over twelve months, you will have reviewed your entire programme systematically without the scramble of an annual panic.
| Approach | Ongoing compliance programme | One-off annual audit |
|---|---|---|
| Risk exposure | Low, with early detection of gaps | High, issues may persist for months |
| Evidence quality | Strong, continuous documentation trail | Patchy, often reconstructed retrospectively |
| Audit readiness | Always audit-ready | Frantic preparation before the audit date |
| Cost | Distributed, predictable investment | Unpredictable, sometimes large reactive costs |
| Staff awareness | High and embedded in culture | Low between audit cycles |
Core actions: Implementing Essential Eight and SMB1001 controls
Now that your programme is scoped and assigned, it’s time to act on best-practice controls. The Essential Eight gives you a clear sequence of actions to follow, and the good news is that even reaching Maturity Level One provides meaningful protection against common attack types.
Here is the recommended action sequence for achieving baseline maturity:
- Enable application control by whitelisting approved software and blocking unapproved executables from running.
- Patch applications promptly. Critical vulnerabilities should be patched within 48 hours and all other patches within two weeks.
- Configure Microsoft Office macro settings to block macros from the internet, which cuts off a common ransomware entry point.
- Harden user applications by disabling unnecessary browser features, PDF viewer capabilities, and internet-facing services.
- Restrict administrative privileges so that only staff who genuinely need admin access have it, and review those permissions every six months.
- Patch operating systems on the same cadence as application patches. Unpatched OS vulnerabilities are a top vector for attackers.
- Implement multi-factor authentication (MFA) for all remote access, cloud services, and privileged accounts.
- Configure daily backups and regularly test restoration to confirm your recovery process actually works.
Vulnerability scans at least fortnightly and annual penetration testing are required for ongoing control performance, according to ACSC guidance. This is not a suggestion, it is a standard you need to meet and document.
Staff training deserves particular attention. Phishing simulations run quarterly help staff recognise social engineering attempts. Incident response drills, even short tabletop exercises, reveal gaps in your plan before a real crisis does. Both activities generate evidence you can show auditors and insurers.
For SMB1001, the Gold tier requires you to document controls, produce evidence of implementation, and engage a qualified assessor. The structured nature of SMB1001 Gold means your evidence portfolio becomes a demonstrable proof point for clients evaluating your security posture. Explore the SMB1001 certification explained in detail to understand what each tier requires.
Pro Tip: Use a centralised compliance register, whether a spreadsheet or dedicated platform, to track every control’s current status, the date it was last reviewed, who owns it, and when the next review is due. This single source of truth saves enormous time during audits.
Where Essential Eight controls are genuinely inappropriate for your environment, compensating or alternate controls may be applied, but they must be assessed and formally approved by an experienced assessor. This is not a loophole to avoid difficult controls. It is a structured process requiring documented justification.
For a deeper look at how these frameworks apply together, the cybersecurity framework for SMBs provides practical context for Queensland businesses navigating both Essential Eight and SMB1001 simultaneously.
Verifying and improving compliance: Assurance, evidence and ongoing review
After putting your controls in place, ongoing verification ensures your compliance posture remains strong and defensible. Queensland’s approach to the Essential Eight actively encourages a risk-based maturity target and continuous governance rather than one-off box ticking. This means your evidence must be current, your reviews must be scheduled, and your improvement actions must be documented.
Follow these steps to maintain ongoing compliance assurance:
- Monitor continuously. Review system alerts, access logs, and patch status at least weekly.
- Scan for vulnerabilities. Run automated vulnerability scans every fortnight and review results promptly.
- Review controls quarterly. Check that existing controls are still appropriate as your business changes.
- Conduct an annual assessment. Engage an assessor or run a structured internal review against your framework of choice.
- Act on findings. Log every gap found, assign an owner, set a remediation deadline, and document when it is resolved.
| Assurance action | Frequency | Sample evidence |
|---|---|---|
| Vulnerability scanning | Fortnightly | Scan reports with timestamps |
| Patch review and application | Ongoing, critical patches within 48 hours | Patch management logs |
| Access privilege review | Every six months | Access review sign-off records |
| Backup restoration test | Quarterly | Test results with date and outcome |
| Staff phishing simulation | Quarterly | Simulation results and training completion |
| Annual penetration test | Annually | Penetration test report and remediation log |
| Full compliance self-assessment | Annually | Self-assessment report and gap action plan |
What counts as real evidence? Auditors, insurers, and regulators want to see timestamped logs, signed reports, and records that cannot easily be fabricated at short notice. Screenshots of system configurations, exported scan reports, meeting minutes from compliance reviews, and training completion certificates all contribute to a credible evidence base.
Common record-keeping mistakes to avoid:
- Storing evidence in email inboxes rather than a dedicated, searchable repository
- Only collecting evidence in the weeks before an audit
- Failing to version your policies and plans so older drafts are lost
- Not recording who approved a risk decision or accepted a residual risk
- Treating incidents as failures to hide rather than learning opportunities to document
Continuous improvement means reviewing your security workflow for SMEs regularly. Each incident, near miss, or failed restoration test is a signal that your controls need adjustment. Capture these lessons formally and update your programme accordingly.
Why a proactive compliance mindset beats the audit rush
Here is something most compliance guides will not tell you directly. The businesses that struggle most with IT compliance are not the ones with the worst security. They are the ones that treat compliance as a problem they deal with in the month before an audit and ignore for the rest of the year.
We have seen this pattern repeatedly with Queensland SMEs. A client realises their controls have drifted after twelve months of no reviews, and they scramble to reconstruct documentation that should have been collected continuously. The irony is that this approach costs more time and money than simply maintaining the records as you go. It also produces evidence that experienced assessors can spot immediately as retrospective, which raises questions about the genuine state of controls.
The shift to a continuous compliance mindset delivers benefits that go beyond simply passing an audit. When your controls are consistently monitored, your team develops genuine security awareness rather than checkbox fatigue. When your documentation is always current, you can respond to a client’s security questionnaire in hours rather than days. When you have a credible evidence trail, winning contracts that require demonstrated security posture becomes a competitive advantage rather than a hurdle.
Contracts are genuinely won and lost on the strength of a business’s security posture. We have seen Queensland SMEs miss out on significant government and enterprise contracts because they could not produce timely, credible compliance evidence. The organisations that win those contracts are not always the ones with the most sophisticated IT infrastructure. They are the ones with clean, continuous documentation and the confidence to demonstrate it.
Our perspective at IT Start is that a detailed practical guide will only get you so far if the underlying mindset is still “compliance as annual event.” The real advantage comes from treating your security programme as a living system that adapts to your business as it grows and as threats evolve.
Enhance your compliance journey with local IT specialists
As you commit to a stronger compliance culture, the right expert support can make all the difference. Managing IT compliance alongside running a business is genuinely demanding, and the technical requirements of Essential Eight and SMB1001 require expertise to implement correctly and maintain consistently.
At IT Start, our business IT support service takes the compliance burden off your shoulders by handling continuous monitoring, patching, and documentation as part of your everyday managed IT arrangement. Our cyber security services are built around the Essential Eight and SMB1001 Gold standard, so you get audit-ready controls, regular reporting, and a clear evidence trail without having to manage it yourself. We also support cloud services that are configured with compliance requirements in mind from day one. Reach out to our Brisbane-based team for a no-pressure compliance consultation and find out exactly where your business stands.
Frequently asked questions
What is the Essential Eight and why is it recommended for Queensland SMEs?
The Essential Eight is a set of practical cyber security controls developed by the ACSC, and the recommended technical benchmark for protecting SME systems across Australia, including Queensland. It provides a structured, prioritised set of actions that address the most common attack vectors.
How often should we review or update our IT compliance controls?
Controls and risks should be reviewed regularly throughout the year, with vulnerability scans fortnightly and formal penetration testing at least annually to maintain ongoing compliance and catch emerging gaps early.
What is SMB1001 certification and why does it matter?
SMB1001 is a structured cyber certification designed specifically for small and medium practices, recommended by Queensland Law Society to help SMEs demonstrate evidence-based cybersecurity to clients and regulators.
If a control isn’t practical for my business, can I skip it?
You can apply alternate controls in place of an unsuitable Essential Eight control, but only after a formal risk decision and approval from an experienced assessor as required by Queensland guidelines.
Does compliance guarantee my business is safe from cyber attacks?
No framework offers total protection, but SMB1001 provides an evidence-based standard that significantly reduces your risk exposure and gives you a strong, defensible foundation should an incident occur.
Recommended
- IT compliance for Queensland SMEs: A practical guide – IT Start
- Understanding IT’s role in compliance for Queensland SMBs – IT Start
- Boost operational efficiency and security with IT compliance – IT Start
- IT compliance for Queensland SMBs: Risks, rewards, and ROI – IT Start
- Why compliance is non-negotiable for high-risk businesses



