TL;DR:
- Changes to privacy laws will soon require nearly all Queensland small businesses to comply.
- The Australian Privacy Principles demand data protection measures like encryption, staff training, and breach response.
- Proactively establishing privacy practices offers a competitive advantage and reduces compliance risks.
Most Queensland small business owners assume the Privacy Act simply does not apply to them. That assumption is about to become very expensive. While businesses under $3 million turnover are currently exempt, sweeping reforms are on track to change the rules for nearly every private business in Australia. This guide breaks down who must comply, what the Australian Privacy Principles actually require, and the practical steps you need to take right now to protect your customers, your reputation, and your business.
Table of Contents
- Who must comply with the Australian Privacy Act?
- The Australian Privacy Principles explained
- Technical and organisational steps to protect personal information
- Privacy obligations and practical compliance for Queensland SMBs
- Why voluntary compliance is smart before the law says you must
- Ready to boost your privacy compliance?
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Who the Act covers | Most Queensland SMBs are exempt—but not for much longer, as reforms arrive in 2026. |
| Privacy Principles matter | The 13 APPs are the compliance heart—covering collection, security, and disclosure. |
| Practical steps matter | Implement encryption, policies, training, and breach response to meet security obligations. |
| Early action is smart | Adopting Privacy Act standards now gives a trust and compliance edge over competitors. |
Who must comply with the Australian Privacy Act?
With the need to prepare established, let’s start by clarifying which Queensland businesses the Act actually covers and why that may soon change.
The Australian Privacy Act 1988 regulates how organisations collect, store, use, and disclose personal information. At its core, the Act applies to what is known as an APP entity, which is any organisation or government agency required to follow the Australian Privacy Principles. For private sector businesses, this generally means annual turnover above $3 million, although the Act also captures certain businesses regardless of size.
Some Queensland SMBs are already covered, even below the $3 million threshold. These include businesses that trade in personal information, run a residential tenancy database, operate a credit reporting function, or provide contracted services to government agencies. Health service providers are also captured regardless of turnover. If your business falls into any of these categories, you have existing, enforceable obligations right now.
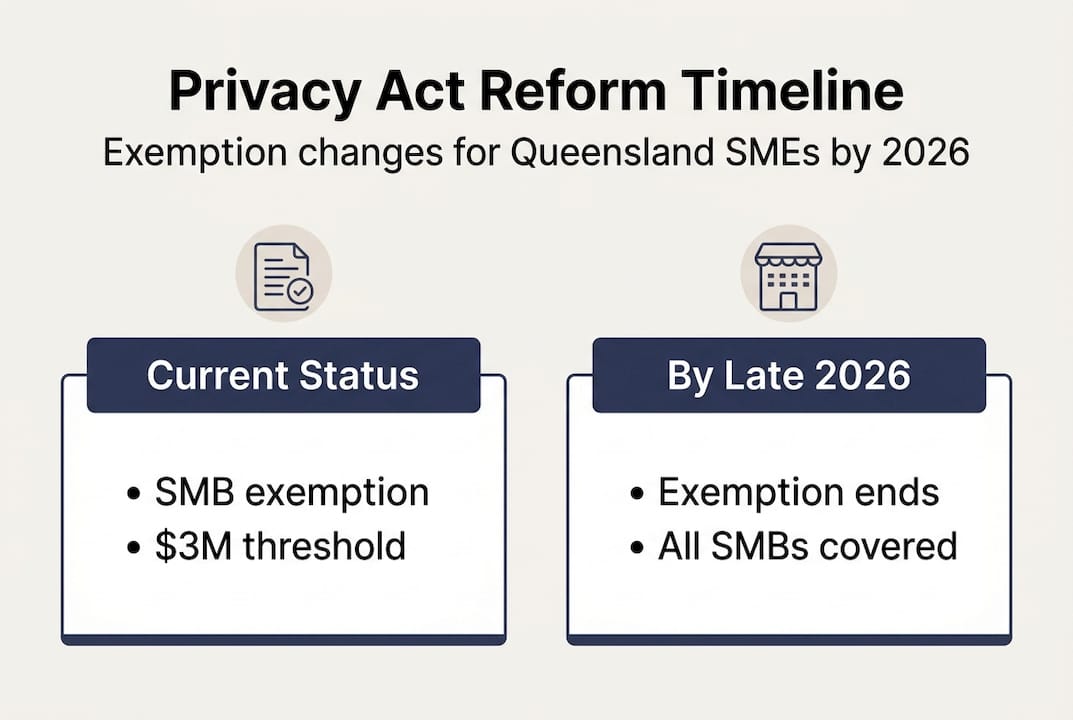
Here is how the current rules compare to what is coming:
| Business type | Currently covered? | Post-reform (late 2026) |
|---|---|---|
| Turnover above $3 million | Yes | Yes |
| Health service provider | Yes | Yes |
| Government contractor | Yes | Yes |
| Trades in personal data | Yes | Yes |
| General SMB under $3 million | No | Very likely yes |
The small business exemption is targeted for removal by late 2026, which means the landscape is shifting dramatically. Approximately 2 million SMBs currently exempt from the Act may lose that status entirely.
This is not a minor administrative change. Once those exemptions are removed, failure to comply could expose your business to significant fines, mandatory breach reporting, and reputational damage. Understanding why data privacy matters now, before enforcement begins, is the smartest move you can make for your business.
The Australian Privacy Principles explained
Once you know whether compliance applies, it is vital to understand what the Act actually requires through the Australian Privacy Principles.
The 13 Australian Privacy Principles form the backbone of privacy law in Australia. They govern everything from how you collect personal information to how you must destroy it. Below is a plain-English summary of all 13:
| APP number | Topic | What it means for your business |
|---|---|---|
| APP 1 | Open and transparent management | Maintain and publish a privacy policy |
| APP 2 | Anonymity and pseudonymity | Let people interact anonymously where possible |
| APP 3 | Collection of solicited information | Only collect what you genuinely need |
| APP 4 | Unsolicited personal information | If you receive info you did not ask for, assess whether you could have collected it lawfully |
| APP 5 | Notification of collection | Tell people what you collect and why |
| APP 6 | Use or disclosure | Only use data for the purpose it was collected |
| APP 7 | Direct marketing | Respect opt-out requests promptly |
| APP 8 | Cross-border disclosure | Protect data sent overseas as if it stayed here |
| APP 9 | Government identifiers | Do not adopt government IDs as your own identifiers |
| APP 10 | Quality of personal information | Keep data accurate and up to date |
| APP 11 | Security | Protect personal information from misuse, loss, and unauthorised access |
| APP 12 | Access | Respond to requests from individuals to access their data |
| APP 13 | Correction | Correct inaccurate personal information on request |
The principles that trip up most SMBs are APP 7 (direct marketing), APP 8 (cross-border data sharing), and APP 11 (security). Specific duties apply for unsolicited information, direct marketing, cross-border transfers, and sensitive data categories like health, financial, and biometric information.
For a practical SMB, here is what “reasonable steps” looks like under APP 11:
- Use secure, password-protected systems for customer data
- Restrict staff access to only the data they need
- Encrypt sensitive files both in storage and in transit
- Have a documented process for destroying data you no longer need
- Train staff on what personal information is and how to handle it
Pro Tip: If your business uses any cloud-based tools like accounting software, CRMs, or HR platforms, check where that data is stored. If servers are overseas, APP 8 may apply, and you need to confirm those overseas providers maintain equivalent protections.

Exploring SMB data protection best practices can help you map which principles are most relevant to your specific operations.
Technical and organisational steps to protect personal information
Knowing the principles is only useful if you can apply them, so next we will cover how SMBs can put robust protections in place.
APP 11 requires both technical and organisational measures for information security. This is not about having perfect systems. It is about taking reasonable steps given the size and nature of your business.
Technical measures every Queensland SMB should have in place:
- Multi-factor authentication (MFA) on all business accounts, especially email and cloud storage
- Encryption for stored customer data and anything sent externally
- Regular automated backups stored separately from primary systems
- Access controls so staff only see the data relevant to their role
- Firewall and endpoint protection on all business devices
- Patch management to keep software updated and vulnerabilities closed
Organisational measures that matter just as much:
- A written data handling policy that staff actually read and sign
- Regular training so employees know what personal information looks like and why it matters
- Vendor assessments before sharing customer data with third-party suppliers
- A clear process for de-identifying or destroying data once it is no longer needed
The Australian Signals Directorate’s Essential Eight framework is an excellent baseline for SMBs. It is not legally required, but aligning with it puts you well above average in terms of security maturity and demonstrates genuine effort to protect personal information.
“Reasonable steps” under the Privacy Act is not defined as perfection. It is proportional to the sensitivity of the information you hold and the size of your business. A small accounting firm holding tax file numbers has a higher bar than a local retailer holding only names and email addresses.
A useful starting point is this secure banking checklist, which covers several overlapping security controls relevant to any business handling sensitive customer information. You should also review your approach to securing cloud data and consider formal guidance on sensitive data protection for higher-risk data categories.
Pro Tip: Do not overlook physical security. Printed customer records left on desks, shared screens in open-plan offices, and unlocked filing cabinets are all genuine privacy risks under the Act.
Privacy obligations and practical compliance for Queensland SMBs
Understanding protections is only the start. Here is how to actually get your business compliant and ready for the future.
Practical compliance means building a documented system, not just good intentions. Start with the following core documents:
- Privacy policy that explains what you collect, how you use it, and how people can access or correct it
- Collection notices provided at the point you gather personal information (web forms, sign-up sheets, contracts)
- Data breach response plan so your team knows exactly what to do if something goes wrong
- Data retention schedule that sets out how long you keep different types of information and how you destroy it
- Staff training records showing team members have been educated on their privacy responsibilities
When a breach does occur, time matters. The Notifiable Data Breaches scheme requires notification to the OAIC and affected individuals if a breach is likely to cause serious harm. Affected businesses must act within 30 days of becoming aware. Failure to notify can result in significant financial penalties, with serious or repeated breaches attracting fines in the millions of dollars.
Signs your business may already be at risk:
- No written privacy policy or one that has not been updated in years
- Staff who do not know what counts as personal information
- Customer data stored in shared spreadsheets with no access restrictions
- Third-party tools used without checking their data handling terms
One often overlooked strategy is voluntarily opting in to OAIC oversight before it becomes mandatory. Businesses that do this signal to clients, partners, and insurers that they take data seriously. In industries like financial services, legal, and healthcare, this is increasingly becoming a point of difference, not just a compliance box. Review IT compliance best practices and how to protect sensitive data for a more structured approach.
Pro Tip: Treat your data breach response plan like a fire drill. Run a tabletop simulation once a year so every team member knows their role before a real incident happens.
Why voluntary compliance is smart before the law says you must
Here is a view that most legal guides will not say out loud: waiting for the law to force you into compliance is one of the most expensive strategies a Queensland SMB can choose.
The businesses that will struggle most in late 2026 are not the ones who lack resources. They are the ones who assumed they had time. Building privacy practices under deadline pressure means rushed documentation, reactive staff training, and patchy technical fixes that leave gaps. Building them now means you get to do it properly, on your terms, with time to embed good habits into your culture.
There is also a commercial argument. Clients in professional services, healthcare, and financial sectors are already asking their suppliers about data practices as part of due diligence. Being able to say “yes, we have a documented privacy programme” is a genuine competitive advantage today. It will become table stakes tomorrow.
We have seen firsthand that businesses using Queensland data protection tips and implementing structured controls early find the process far less disruptive than those scrambling to comply after a breach or a regulatory change. Privacy is not a burden. It is a signal to your market that you are a business worth trusting.
Ready to boost your privacy compliance?
If this guide has made one thing clear, it is that privacy compliance is no longer a “later” problem for Queensland SMBs. The reforms are coming, the obligations are real, and the penalties for getting it wrong are significant. IT Start works with Brisbane businesses every day to build practical, audit-ready privacy and security frameworks that actually fit how you operate. From documentation and staff training to technical controls and breach response planning, our team covers it all. Explore our business IT support services or learn about our dedicated cyber security services to take the next step with a local team that understands Queensland business.
Frequently asked questions
Are all Queensland SMBs still exempt from the Privacy Act?
Most are currently exempt if their turnover is under $3 million, but the exemption removal is targeted for late 2026, which means almost every private business in Queensland will need to comply.
What personal information security steps meet the Privacy Act?
APP 11 requires technical measures like encryption and access controls, plus organisational steps like staff training, and you must also destroy or de-identify data once it is no longer needed.
How do I notify about data breaches under the Act?
Under the Notifiable Data Breaches scheme, eligible breaches must be reported to the OAIC and affected individuals within 30 days, and serious or repeated failures can attract fines in the millions.
Does Queensland state law add extra requirements?
Federal privacy law applies to private sector SMBs, while Queensland’s Information Privacy Act only covers state public sector agencies, so there are no additional state-level requirements for private businesses.
Recommended
- SMB data protection best practices for Queensland businesses – IT Start
- How to keep data safe and secure: 85% fewer breaches for Queensland SMEs – IT Start
- Understanding IT’s role in compliance for Queensland SMBs – IT Start
- How to secure data in cloud computing for Queensland SMEs – IT Start
- What is business security? Bristol’s essential guide
- Your Guide to Managed Security Services for Small Business – Heights Consulting Group



