Many Queensland business owners believe cybersecurity frameworks are only necessary for large corporations with extensive IT departments and unlimited budgets. This misconception leaves small to medium-sized businesses dangerously exposed to cyber threats that can devastate operations, compromise client data, and destroy hard-earned reputations. The reality is that cybersecurity frameworks reduce successful attacks by 60% for SMBs, making them essential tools for businesses of all sizes. This article will guide you through understanding frameworks, selecting the right one for your Queensland business, and implementing practical security measures that protect your operations without breaking the bank.
Table of Contents
- Understanding Cybersecurity Frameworks And Why They Matter For SMBs
- How Cybersecurity Frameworks Improve Your IT Security Posture
- Key Cybersecurity Frameworks For Queensland SMBs And How To Choose
- Practical Steps To Implement And Maintain Your Cybersecurity Framework
- Discover Expert Cybersecurity Support Tailored For Queensland SMBs
Key takeaways
| Point | Details |
|---|---|
| Attack reduction | Cybersecurity frameworks reduce successful cyberattacks on SMBs by 60% through structured controls |
| Incident prevention | Implementing frameworks cuts security incidents by 30 to 40% by hardening systems and processes |
| Compliance support | Frameworks help Queensland SMBs meet regulatory requirements efficiently and demonstrate due diligence |
| Risk-based approach | Resource-limited SMBs should prioritise framework elements based on assessed risks for maximum impact |
| Human factor | Employee training and awareness programmes are critical success factors for any framework implementation |
Understanding cybersecurity frameworks and why they matter for SMBs
A cybersecurity framework is a structured set of policies, controls, and practices designed to manage and reduce cyber risks systematically. Think of it as a comprehensive blueprint that guides your business through identifying vulnerabilities, implementing protective measures, detecting threats, responding to incidents, and recovering from attacks. These frameworks aren’t abstract concepts reserved for enterprise IT departments. They’re practical roadmaps that help Queensland SMBs build resilient security postures without requiring massive technical expertise or budgets.
Several frameworks suit SMB needs particularly well. The Essential Eight, developed by the Australian Cyber Security Centre, provides eight foundational mitigation strategies that address the most common attack vectors facing Australian businesses. The NIST Cybersecurity Framework offers a flexible, risk-based approach organised around five core functions: Identify, Protect, Detect, Respond, and Recover. ISO 27001 provides an internationally recognised standard for information security management systems, ideal for SMBs seeking formal certification or working with clients who require demonstrated compliance.
The myth that only large organisations need frameworks has been thoroughly debunked by recent threat data. SMBs now represent prime targets for cybercriminals precisely because they often lack robust defences whilst holding valuable customer data, financial information, and intellectual property. Research shows that implementing a cybersecurity framework reduces successful attacks by 60% for small to medium-sized businesses, making adoption a business-critical decision rather than an optional luxury.
Queensland SMBs face particular challenges in the current threat landscape. Local businesses handle sensitive client information across industries like financial services, healthcare, legal practices, and professional services. A single data breach can trigger regulatory penalties, client lawsuits, and irreparable reputation damage. Understanding why SMB cybersecurity matters helps contextualise the urgent need for structured protection.
Pro Tip: Start by conducting a simple risk assessment to identify your most valuable digital assets and the threats they face, then select framework elements that address your highest risks first.
“Cybersecurity frameworks transform security from reactive firefighting into proactive risk management, giving SMBs the structure needed to defend against evolving threats systematically.”
The key takeaway is that frameworks provide proven, tested approaches developed by security experts and refined through real-world application. Rather than reinventing security practices from scratch, Queensland SMBs can leverage these established blueprints to build effective defences efficiently. The question isn’t whether your business needs a framework, but which one aligns best with your specific risks, resources, and compliance obligations.
How cybersecurity frameworks improve your IT security posture
Cybersecurity frameworks strengthen your IT security posture by providing comprehensive controls that span every aspect of your digital environment. These structured approaches cover asset management, user access controls, network monitoring, vulnerability management, incident response procedures, and business continuity planning. Rather than implementing random security tools without coordination, frameworks ensure all protective measures work together as an integrated defence system.
The measurable improvements are substantial. Studies demonstrate that frameworks reduce security incidents by 30 to 40% for organisations that implement them properly. This reduction stems from multiple factors: better visibility into your IT environment, standardised security processes that eliminate gaps, regular monitoring that catches threats early, and documented procedures that ensure consistent responses to incidents.
Frameworks institutionalise best practices throughout your organisation. Security becomes embedded in daily operations rather than treated as an afterthought or handled inconsistently by different staff members. Employee responsibilities become clearly defined, technical controls are systematically maintained, and leadership receives regular reporting on security posture and emerging risks. This cultural shift transforms security from an IT problem into a business-wide priority that everyone understands and supports.
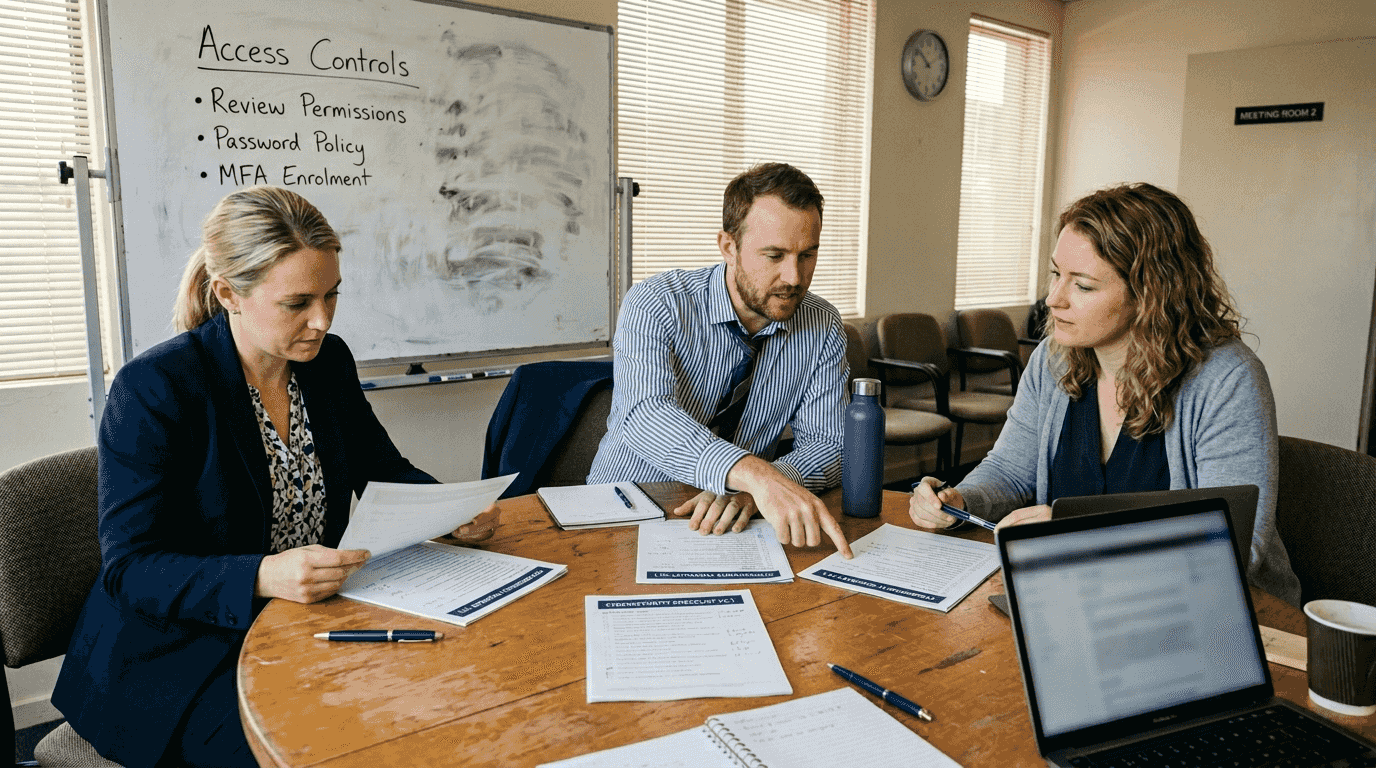
Practical improvements manifest across multiple areas. Access controls ensure only authorised personnel can reach sensitive systems and data. Patch management processes keep software updated against known vulnerabilities. Backup procedures protect against ransomware and data loss. Network segmentation limits how far attackers can move if they breach perimeter defences. Logging and monitoring provide early warning of suspicious activities before they escalate into full breaches.
The continuous improvement cycle built into frameworks drives ongoing security enhancements. Regular reviews identify new risks, assess control effectiveness, and adapt defences to emerging threats. This iterative approach means your security posture strengthens over time rather than becoming outdated as attack methods evolve. Queensland SMBs that embrace security frameworks gain resilience that compounds annually.
Key security posture improvements include:
- Reduced attack surface through systematic vulnerability management and patching
- Faster threat detection via continuous monitoring and automated alerting systems
- Minimised breach impact through network segmentation and access restrictions
- Improved incident response with documented procedures and defined roles
- Enhanced compliance demonstration through standardised controls and audit trails
- Stronger vendor security via third-party risk assessment processes
Pro Tip: Review and update your framework implementation quarterly to address new threats, incorporate lessons from security incidents, and adjust controls as your business evolves.
Frameworks also provide objective metrics for measuring security effectiveness. Rather than guessing whether your defences are adequate, you can track specific indicators like time to detect threats, percentage of systems patched within target timeframes, user security awareness scores, and incident response times. These metrics enable data-driven decisions about where to invest limited security resources for maximum impact.
Key cybersecurity frameworks for Queensland SMBs and how to choose
Selecting the right cybersecurity framework requires understanding how different approaches align with your business size, industry requirements, available resources, and compliance obligations. Queensland SMBs benefit most from frameworks that deliver strong protection without overwhelming limited IT staff or budgets. Three frameworks stand out as particularly relevant: Essential Eight, NIST Cybersecurity Framework, and ISO 27001.
The Essential Eight framework provides foundational mitigation strategies specifically designed for Australian organisations. Developed by the Australian Cyber Security Centre, it focuses on eight critical controls that address the most common attack methods: application whitelisting, patching applications and operating systems, restricting administrative privileges, multi-factor authentication, and regular backups. This framework offers practical, achievable security improvements ideal for SMBs beginning their cybersecurity journey.
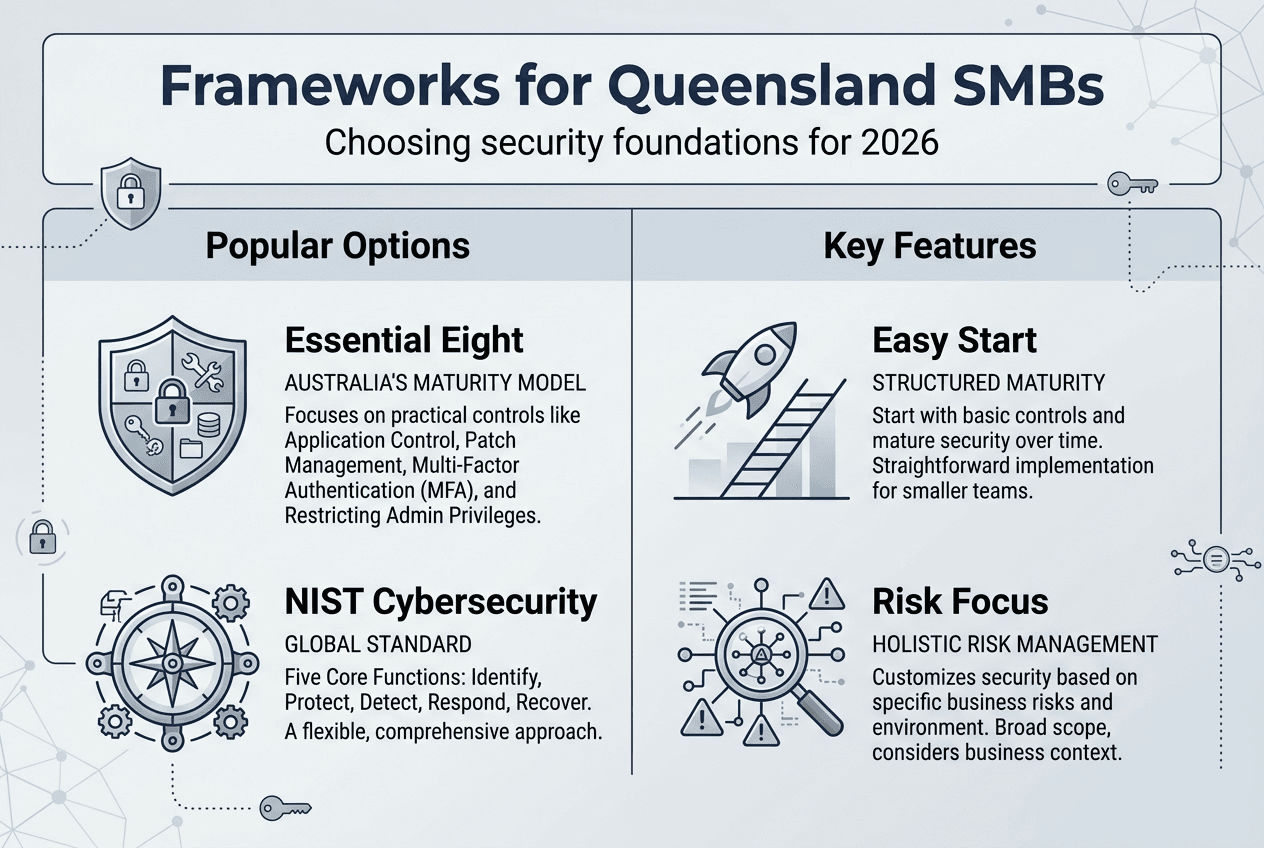
The NIST Cybersecurity Framework takes a risk-based approach organised around five core functions. It helps organisations identify assets and risks, protect critical systems, detect security events, respond to incidents effectively, and recover operations quickly. This flexibility makes NIST CSF suitable for growing SMBs that need comprehensive coverage without rigid implementation requirements. The framework scales well as businesses expand and security needs become more complex.
ISO 27001 provides an internationally recognised standard for information security management systems. It requires formal documentation, regular audits, and certification processes that demonstrate robust security practices to clients, partners, and regulators. Queensland SMBs in industries like financial services, healthcare, or legal practices often pursue ISO 27001 to meet client expectations and regulatory requirements whilst building genuinely strong security programmes.
| Framework | Key Features | Complexity | Cost | Best For |
|---|---|---|---|---|
| Essential Eight | Eight foundational controls, maturity levels, Australian focus | Low to Medium | Low | SMBs starting cybersecurity journey, government contractors |
| NIST CSF | Five core functions, flexible implementation, comprehensive coverage | Medium | Low to Medium | Growing SMBs needing scalable risk management |
| ISO 27001 | Formal certification, documented ISMS, international recognition | High | Medium to High | SMBs requiring compliance proof, international clients |
Choosing the right framework depends on several factors. Consider your business size and available IT resources. A five-person firm needs different approaches than a 50-employee organisation with dedicated IT staff. Evaluate your industry’s compliance requirements. Healthcare providers face different regulatory obligations than retail businesses. Assess your client expectations. Do contracts require specific certifications or security standards?
Risk profile plays a crucial role in framework selection. Businesses handling sensitive personal information, financial data, or intellectual property need more comprehensive controls than those with minimal data exposure. Budget constraints matter too. Some frameworks require minimal investment beyond staff time, whilst others involve certification costs, consultant fees, and specialised tools.
Many Queensland SMBs benefit from starting with the Essential Eight to build foundational protections quickly, then layering additional controls from NIST CSF as they mature. This progressive approach delivers immediate risk reduction whilst building toward more comprehensive security over time. Businesses can later pursue ISO 27001 certification if client requirements or competitive positioning demands formal validation.
The comparison of cybersecurity solutions helps clarify which framework elements address your specific vulnerabilities most effectively. Focus on frameworks that align with your business goals rather than chasing certifications that don’t deliver practical value. The best framework is one you’ll actually implement and maintain consistently, not the most impressive-sounding option that overwhelms your resources.
Practical steps to implement and maintain your cybersecurity framework
Implementing a cybersecurity framework successfully requires systematic planning, stakeholder engagement, and realistic expectations about timelines and resources. Queensland SMBs can achieve strong security outcomes by following a structured approach that prioritises high-impact controls and builds momentum through early wins.
-
Conduct a comprehensive risk assessment to identify your most valuable assets, likely threats, existing vulnerabilities, and potential business impacts from security incidents. Document findings clearly so everyone understands what you’re protecting and why.
-
Select the framework that best matches your risk profile, compliance needs, available resources, and business objectives. Don’t choose based on what competitors use or what sounds most impressive. Pick the approach you can realistically implement and sustain.
-
Develop an implementation roadmap that prioritises controls addressing your highest risks first. Resource-limited SMBs must prioritise based on risk to maximise protection from limited budgets. Quick wins like multi-factor authentication and regular backups deliver immediate value whilst you work toward more complex controls.
-
Engage employees through comprehensive training programmes that explain why security matters, what threats you face, and how their actions protect or endanger the business. Make training practical, relevant, and ongoing rather than annual tick-box exercises.
-
Implement technical controls systematically, testing each thoroughly before moving to the next. Document configurations, update procedures, and train staff on new tools as you deploy them. Rushing implementation creates gaps and confusion that undermine security.
-
Establish monitoring and reporting processes that provide visibility into security posture, detect anomalies quickly, and keep leadership informed about risks and incidents. Regular metrics help demonstrate progress and justify continued investment.
-
Schedule regular reviews to assess control effectiveness, identify new risks, update policies, and adapt to evolving threats. Cybersecurity isn’t a one-time project but an ongoing programme requiring continuous attention.
Employee awareness represents a critical success factor often underestimated by SMBs focused on technical controls. Your staff are both your greatest vulnerability and your strongest defence. Phishing attacks, weak passwords, and careless data handling cause more breaches than sophisticated hacking. Investing in cyber security awareness programmes pays dividends through reduced incidents and faster threat reporting.
Pro Tip: Conduct quarterly tabletop exercises where staff walk through responding to realistic scenarios like ransomware attacks or data breaches, identifying gaps in procedures and building confidence before real incidents occur.
Budget constraints require creative approaches to framework implementation. Many controls cost little beyond staff time: updating policies, restricting administrative access, enabling multi-factor authentication, and conducting security awareness training. Focus these low-cost, high-impact measures first. As budget allows, add tools for monitoring, backup, and advanced threat protection.
Maintaining your framework over time requires discipline and accountability. Assign clear ownership for each control area. Schedule regular policy reviews. Track compliance metrics. Conduct periodic audits to verify controls work as intended. Treat security as a business process requiring the same rigour as financial management or quality control.
Adapting to evolving threats means staying informed about emerging attack methods, new vulnerabilities affecting your technology stack, and changing compliance requirements. Subscribe to security advisories from vendors and industry groups. Participate in local business security forums. Engage with managed security providers who monitor threat landscapes professionally and can advise on necessary adjustments.
Discover expert cybersecurity support tailored for Queensland SMBs
Navigating cybersecurity frameworks and implementing robust protections can feel overwhelming when you’re focused on running your business. IT Start specialises in helping Queensland SMBs build and maintain strong security postures through expert guidance, managed services, and tailored solutions that fit your budget and business needs. Our team brings deep expertise in Essential Eight implementation, risk assessments, compliance support, and ongoing security monitoring designed specifically for small to medium-sized businesses.
We understand the unique challenges facing Brisbane businesses: limited IT resources, tight budgets, complex compliance requirements, and the need to balance security with operational efficiency. Our cyber security services provide comprehensive protection including vulnerability assessments, framework implementation, staff training, incident response planning, and 24/7 monitoring. We also offer cloud services that enhance security through enterprise-grade infrastructure, automated backups, and disaster recovery capabilities.
Pro Tip: Engage with cybersecurity experts early in your framework journey to avoid common implementation pitfalls, accelerate deployment timelines, and ensure controls are configured optimally for your specific environment.
Contact IT Start today for a complimentary security assessment that identifies your current risks and provides a clear roadmap for strengthening your cybersecurity posture through proven frameworks and practical controls.
FAQ
What is a cybersecurity framework and why does my SMB need one?
A cybersecurity framework is a structured set of guidelines, controls, and best practices designed to help organisations manage cyber risks systematically. Your SMB needs one because frameworks provide proven approaches to protecting data, preventing breaches, ensuring business continuity, and demonstrating compliance with regulatory requirements. Without a framework, security efforts remain ad hoc and ineffective against sophisticated threats.
Which cybersecurity framework is best suited for small to medium-sized businesses in Queensland?
The Essential Eight framework is ideal for Queensland SMBs seeking foundational protections with clear, achievable implementation steps and maturity levels. NIST Cybersecurity Framework suits growing businesses needing comprehensive, flexible risk management that scales with expansion. ISO 27001 works best for SMBs requiring formal certification to meet client expectations or regulatory obligations in industries like finance, healthcare, or legal services.
How can I ensure my employees follow cybersecurity best practices consistently?
Regular training sessions and practical awareness programmes help employees understand threats and their role in prevention. Leadership involvement signals that security is a business priority, not just an IT concern. Use simple, clear policies that explain what to do and why, then reinforce through ongoing communication, simulated phishing exercises, and recognition of good security behaviours.
What are the immediate steps to take if my SMB experiences a cyber incident?
Isolate affected systems immediately to prevent the breach from spreading across your network. Contact your IT security expert or managed service provider to begin investigation and containment. Notify relevant stakeholders including clients, partners, and regulators as required by law and contracts. After resolving the incident, review what happened and strengthen framework controls to prevent recurrence.



