Queensland business owners face a stark reality in 2026: phishing attacks increased by 350% during the pandemic’s shift to remote work, and cybercriminals continue exploiting weak security. Remote work security protects your data, networks, and devices when employees operate outside the office. Without layered defenses, your business risks breaches, compliance penalties, and operational chaos. This guide delivers practical strategies across technology, people, and legal compliance to secure your remote workforce effectively.
Table of Contents
- Understanding Remote Work Security: Definition And Importance
- Regulatory Context: Queensland And Australian Privacy Requirements
- Remote Work Threat Landscape: Common Attack Vectors
- Critical Technologies For Remote Security: Access, Network, And Endpoint Protection
- Essential Security Practices: Employee Training, Patch Management, And Incident Response
- Leveraging Managed IT Services For Remote Work Security
- Summary And Practical Next Steps For Queensland Business Owners
- Enhance Your Remote Work Security With IT Start’s Managed IT Services
Key Takeaways
| Point | Details |
|---|---|
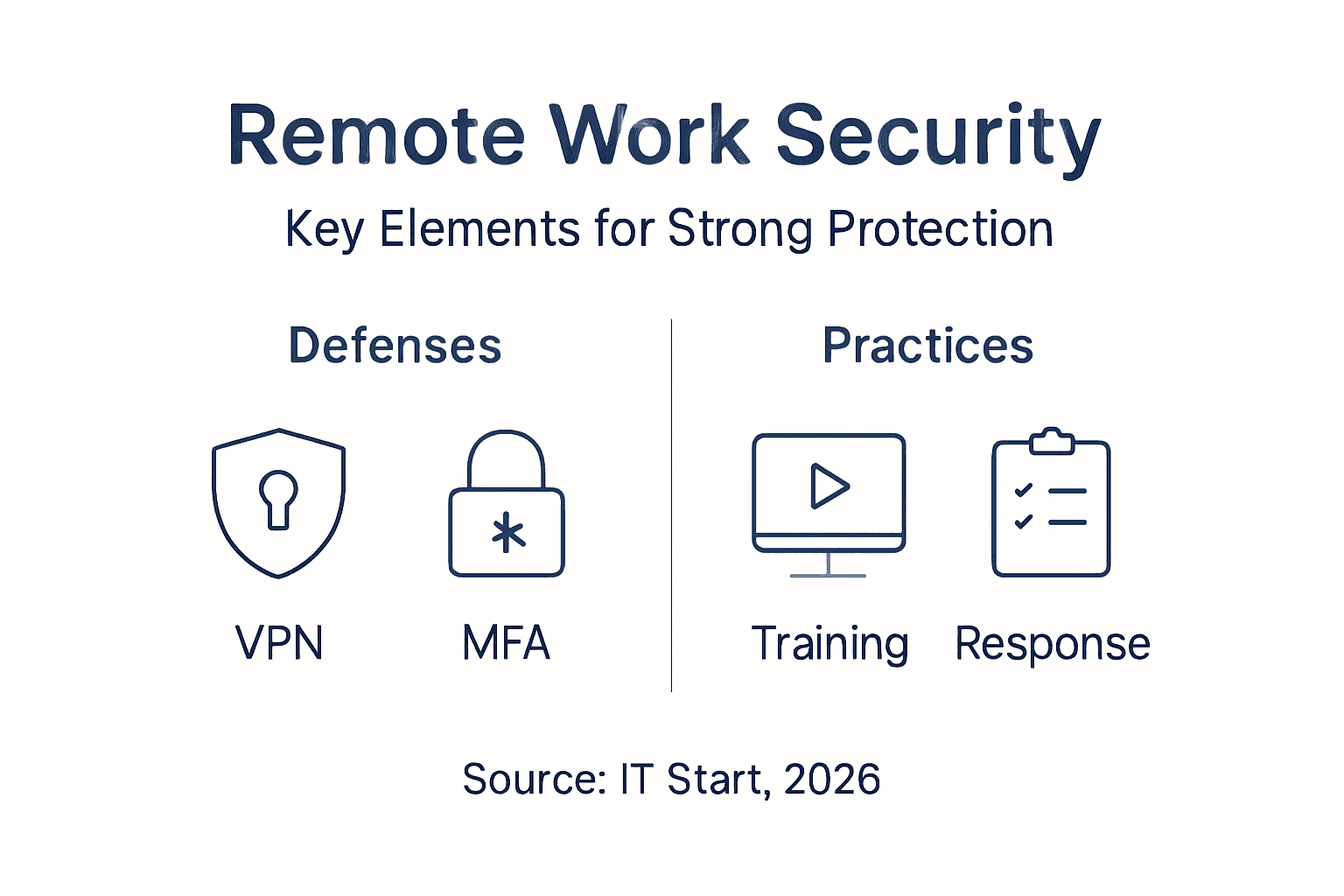
| Remote work security requires layered defenses | Technology, employee training, and compliance must work together to prevent breaches. |
| Phishing attacks surged 350% globally | Remote workers are prime targets for credential theft and social engineering attacks. |
| Queensland SMEs must comply with privacy laws | Australian Privacy Principles and Queensland Information Privacy Act mandate secure data handling. |
| Multi-factor authentication stops 99.9% of breaches | MFA and VPNs are essential technical controls for remote access security. |
| Employee training reduces incidents by 40% | Regular security awareness programs significantly lower successful attacks. |
Understanding Remote Work Security: Definition and Importance
Remote work security means protecting data, networks, and devices accessed from outside your central office. It involves three main components: data integrity ensures information stays accurate and confidential, network safety protects communication channels, and endpoint defenses secure laptops and mobile devices. Queensland SMEs face heightened risks due to limited IT staff and increasing cyber threats targeting remote setups.
Proper security enables productivity without compromising confidentiality or compliance. Remote work can be as secure as on-premises work with proper policies, VPNs, MFA, and endpoint protections according to Cyber.gov.au. Essential protective measures include:
- VPNs create encrypted tunnels between remote workers and company networks
- Multi-factor authentication adds verification layers beyond passwords
- Endpoint security software protects devices from malware and unauthorized access
- Regular security audits identify vulnerabilities before attackers exploit them
Pro Tip: Start with work from home security steps that address your most critical assets first. Map where sensitive data lives, who accesses it remotely, and which devices connect to your network. This baseline assessment guides your security investments.
Regulatory Context: Queensland and Australian Privacy Requirements
The Privacy Act 1988 and Australian Privacy Principles regulate data handling and remote access security across Australia. These national standards require businesses to protect personal information, notify affected parties of data breaches, and maintain secure systems. Queensland’s Information Privacy Act adds specific provisions for public sector entities and influences private compliance considerations.
Compliance requires secure handling of remote access data and clear breach notification procedures. SMEs must implement policies that reflect these laws when enabling remote work. Your obligations include:
- Conducting privacy impact assessments before deploying remote work technology
- Encrypting data in transit and at rest
- Maintaining audit logs of remote access activities
- Training employees on lawful data handling practices
Failing to comply can result in fines up to $2.5 million for serious violations, reputational damage that drives customers away, and operational disruption during investigations. The Australian Privacy Principles framework provides clear guidance on building compliant remote work policies.
Remote Work Threat Landscape: Common Attack Vectors
Alarming Statistic: Phishing attacks increased by 350% globally during the COVID-19 pandemic era, exploiting remote work vulnerabilities that persist in 2026. Cybercriminals target remote workers because home networks often lack enterprise-grade protections. Insecure home Wi-Fi networks and use of personal devices increase exposure dramatically.
Typical attack vectors include:
- Email scams impersonating executives or vendors to steal credentials
- Credential theft through fake login pages and keylogger malware
- Malware infection via malicious attachments and compromised websites
- Man-in-the-middle attacks on unsecured Wi-Fi connections
Small businesses often lack layered defenses, making them attractive targets for automated attacks and opportunistic criminals. Understanding these threats is crucial to prioritizing effective security measures. Attackers exploit trust, urgency, and technical gaps. They know remote workers may click suspicious links when distracted or working odd hours without IT support nearby.
Critical Technologies for Remote Security: Access, Network, and Endpoint Protection
VPNs create encrypted tunnels securing data traffic between remote users and company networks, preventing eavesdropping and tampering. Multi-factor authentication can stop 99.9% of remote work account breaches by requiring two or more verification factors. Authenticator apps and hardware tokens are best options because they resist phishing better than SMS codes.
Endpoint security includes antivirus software, device encryption, and cloud-managed protection suites that update automatically. Cyber security solutions integrate these technologies into unified platforms.
| Security Layer | Technology Options | Key Benefits | Implementation Complexity |
|---|---|---|---|
| Network Security | VPN, Zero Trust Network Access | Encrypts traffic, validates every connection | Medium |
| Access Control | MFA via app/hardware token | Stops 99.9% of credential attacks | Low |
| Endpoint Protection | Cloud antivirus, EDR, encryption | Protects devices, detects threats | Medium |
Pro Tip: Prioritize MFA implementation before enabling remote access to prevent most common breaches. Deploy it first for email and critical business applications. Roll out VPN access second, then enhance endpoint protections third. This sequence addresses the highest-risk gaps quickly.
Essential Security Practices: Employee Training, Patch Management, and Incident Response
SMEs with dedicated security training see 40% fewer incidents, proving training is critical to reducing risk. Employee training reduces successful phishing and social engineering attacks significantly by building awareness to recognize scams and follow security protocols. Training transforms staff from vulnerabilities into your first line of defense.
60% of breaches exploit unpatched software vulnerabilities, making timely patch management essential. Patch management ensures vulnerabilities are fixed promptly to close exploitable gaps before attackers strike. Incident response plans tailored for remote scenarios speed breach detection and containment, minimizing damage.
- Schedule quarterly security awareness training covering phishing recognition, password hygiene, and safe remote work practices
- Enforce automated update policies for operating systems and business applications
- Test incident response plans twice yearly with simulated breach scenarios involving remote workers
- Establish clear escalation procedures so remote employees know how to report suspicious activity
Pro Tip: Simulated phishing tests improve employee vigilance effectively. Send fake phishing emails quarterly and provide immediate feedback to employees who click. This hands-on learning reinforces training concepts without real risk.
Leveraging Managed IT Services for Remote Work Security
Managed IT services provide 24/7 proactive monitoring and automated patch management that small internal teams cannot match. They help achieve and maintain compliance with Queensland and Australian regulations through expert guidance and regular policy updates. Access to cybersecurity experts reduces operational complexity and enhances defenses without hiring full-time security staff.
Cost-effective for SMEs by leveraging economies of scale and advanced tools, managed IT security for Brisbane SMEs delivers enterprise-grade protection at predictable monthly costs. Key service benefits include:
- Expert guidance on security strategy tailored to your business
- Rapid incident response when breaches occur, minimizing downtime
- Compliance updates ensuring policies match evolving regulations
- Cost savings compared to building equivalent in-house capabilities
Managed providers deploy tools like SIEM systems, endpoint detection and response platforms, and vulnerability scanners that would be prohibitively expensive for individual SMEs. The managed security service workflow demonstrates how continuous monitoring catches threats early. Providers also maintain relationships with law enforcement and regulatory bodies, streamlining breach reporting.
Summary and Practical Next Steps for Queensland Business Owners
Remote work security rests on three pillars: technology protects systems, people follow safe practices, and compliance ensures legal alignment. These pillars form an integrated security posture stronger than any single measure. Assess your current remote work setup by identifying which assets employees access remotely and what controls currently protect them.
Review compliance with applicable laws and align policies accordingly to avoid penalties. Implement layered protections addressing the full attack surface:
- Deploy VPN access for all remote connections to encrypt network traffic
- Enforce multi-factor authentication on email, file storage, and business applications
- Install endpoint security software on all devices accessing company data
- Train employees quarterly on phishing recognition and security best practices
- Establish automated patch management processes to close vulnerabilities promptly
- Create and test incident response procedures covering remote work scenarios
- Partner with managed IT providers for ongoing security support and expert guidance
These steps transform reactive security into proactive defense. Contact IT Start for a free security assessment that identifies your specific vulnerabilities and prioritizes remediation based on risk and budget.
Enhance Your Remote Work Security with IT Start’s Managed IT Services
IT Start offers comprehensive managed IT and support services and cyber security solutions tailored for Queensland SMEs navigating remote work challenges. Our services include proactive 24/7 monitoring, expert patch management, compliance assistance with Australian privacy laws, and rapid incident response. We help you reduce cyber risks while focusing on your core business operations.
Partnering with IT Start means accessing enterprise-grade security tools and certified experts without the cost of building an internal team. Contact us today to safeguard your remote workforce with trusted technology and ongoing support designed for Brisbane businesses.
Frequently Asked Questions
What is remote work security?
Remote work security is the practice of protecting company data, networks, and devices accessed by employees working outside the office to prevent cyber threats and ensure compliance. The goal is to maintain confidentiality, integrity, and availability regardless of location. This includes technical measures like VPNs and MFA, employee training on safe practices, and adherence to privacy laws.
How can Queensland SMEs comply with privacy laws while enabling remote work?
SMEs must follow the Privacy Act 1988 and Queensland Information Privacy Act by implementing secure remote access controls, proper data handling policies, and breach notification procedures. Regular compliance reviews and employee training ensure ongoing adherence. Conducting privacy impact assessments before deploying new remote work technology helps identify and address compliance gaps proactively.
What technologies are essential for securing remote work?
Essential technologies include multi-factor authentication to prevent unauthorized access, VPNs to encrypt network traffic, and endpoint security software for device protection. Adopting these tools dramatically reduces breach risks by addressing the most common attack vectors. Cloud-managed security platforms simplify deployment and maintenance for SMEs with limited IT staff.
Why is employee security training critical for remote work?
Employee training builds awareness to recognize phishing scams and follow security protocols, significantly lowering successful attacks by up to 40%. Trained staff make better decisions that protect company assets even outside the office. Regular training sessions and simulated phishing tests reinforce safe behaviors and keep security awareness high as threats evolve.



